Update: 1768.py Version 0.0.15 Some new features that help with analyzing memory d 2022-8-18 06:30:30 Author: blog.didierstevens.com(查看原文) 阅读量:41 收藏
Update: 1768.py Version 0.0.15
Some new features that help with analyzing memory dumps.
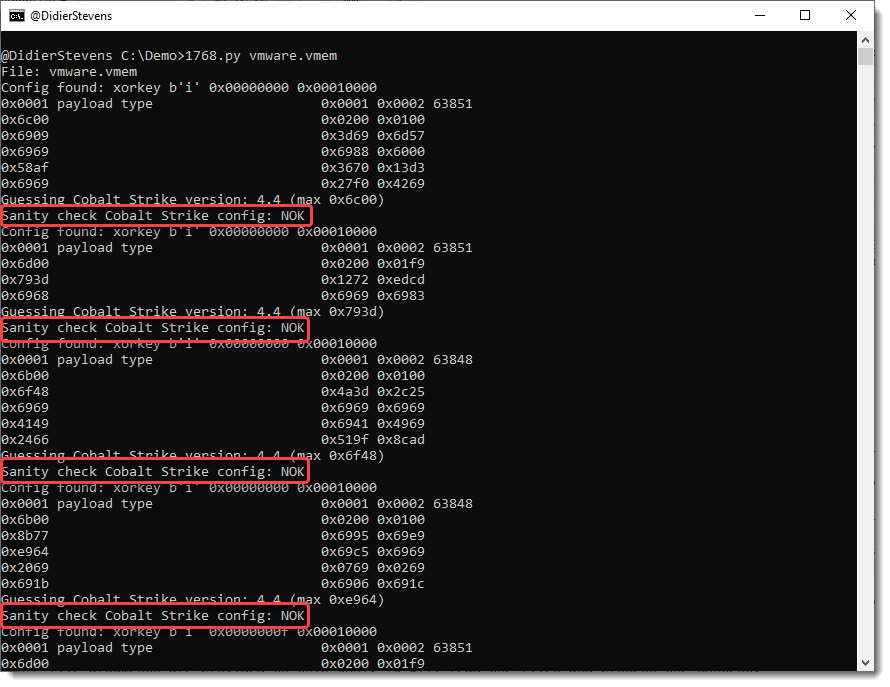
Here is the analysis of a VMware vmem file:

There’s a new sanity check, determining if an extracted configuration is OK or not OK (NOK).
A config passes the sanity check if it contains a valid payload type and a valid public key.
Configurations that don’t pass the sanity check, are most likely false positives: they have a valid header, but no valid fields. They can show up in memory dumps of Windows machines.
Option -S can be used to hide configurations that don’t pass the sanity check:

Now we are just left with detections of the sleep mask routine. What’s new in this version, is that the position where the signature was found is listed.
Finding both 32-bit and 64-bit routines is unusual.
Option -V can be used to dump 256 bytes before and after the signature, to help us get an idea what we are dealing with.

And what we actually found here, is the memory of the anti-virus program containing signatures, like signatures for Cobalt Strike sleep mask deobfuscation routines.
1768_v0_0_15.zip (http)
MD5: 15EBA21D59D78ED9A674DC2B88687555
SHA256: 73987F1B8577A5C31B2D7BDC197A465F8700B3F3C7838A31802BD77FFC872C42
No comments yet.
如有侵权请联系:admin#unsafe.sh