2024-12-11 20:17:43 Author: securityaffairs.com(查看原文) 阅读量:8 收藏
Operation Digital Eye: China-linked relies on Visual Studio Code Remote Tunnels to spy on Europen entities
Pierluigi Paganini
December 11, 2024

An alleged China-linked APT group targeted large business-to-business IT service providers in Southern Europe as part of Operation Digital Eye campaign.
Between late June and mid-July 2024, a China-linked threat actor targeted major IT service providers in Southern Europe in a campaign codenamed ‘Operation Digital Eye.’ Cyberspies aimed to establish footholds and compromise downstream entities but were detected and halted early by SentinelOne and Tinexta Cyber.
In “Operation Digital Eye,” threat actors employed lateral movement techniques linked to a shared vendor or “digital quartermaster” within the Chinese APT ecosystem. The researchers noticed that the attackers exploited Visual Studio Code and Microsoft Azure for command-and-control (C2), in an attempt to avoid detection. This campaign is the first observed case of a suspected Chinese APT group abusing Visual Studio Code for C2 operations, marking a significant shift in tactics.
“The attack campaign, which we have dubbed Operation Digital Eye, took place from late June to mid-July 2024, lasting approximately three weeks.” reads the report published by SentinelLabs “The targeted organizations provide solutions for managing data, infrastructure, and cybersecurity for clients across various industries, making them prime targets for cyberespionage actors.”
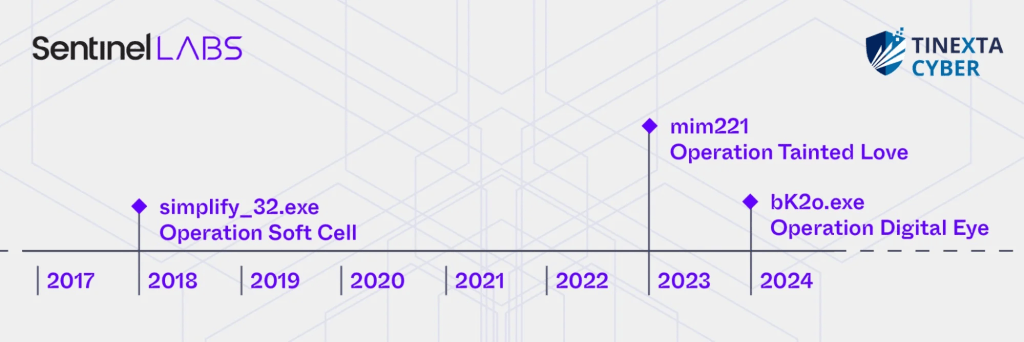
The group behind “Operation Digital Eye” remains unidentified due to the shared nature of malware, tools, and techniques, tactics and procedures (TTPs) within the Chinese cyber threat ecosystem. The attackers employed a pass-the-hash capability linked to custom Mimikatz modifications, known as mimCN, which are uniquely tied to Chinese cyberespionage campaigns such as “Operation Soft Cell” and “Operation Tainted Love.” These tools have connections to multiple Chinese APT groups, highlighting a collaborative infrastructure within the ecosystem.

“The abuse of Visual Studio Code Remote Tunnels for C2 purposes is central to this campaign. Originally designed to enable remote development, this technology provides full endpoint access, including command execution and filesystem manipulation.” SentinelOne and Tinexta Cyber researchers Aleksandar Milenkoski and Luigi Martire said. “Additionally, Visual Studio Code tunneling involves executables signed by Microsoft and Microsoft Azure network infrastructure, both of which are often not closely monitored and are typically allowed by application controls and firewall rules. As a result, this technique may be challenging to detect and could evade security defenses.”
State-sponsored hackers exploit public cloud infrastructure to camouflage their activity within regular network traffic and use legitimate tools to evade detection. Initial breaches often involve SQL injection attacks against internet-facing applications and databases, automated by tools like SQLmap. Post-infiltration, attackers deploy a PHP-based web shell, PHPsert, for persistent remote access. Follow-up actions include reconnaissance, credential theft, and lateral movement via RDP and pass-the-hash techniques.
Attackers utilized SSH and Visual Studio Code Remote Tunnels for executing commands on compromised systems, authenticating via GitHub accounts to establish remote connections through vscode.dev. It’s unclear if the accounts used were newly created or previously compromised.
The attackers strategically utilized infrastructure exclusively within Europe, including services from M247 and Microsoft Azure. This strategy aimed to reduce suspicion by aligning the location of their infrastructure with that of their European targets. By leveraging widely trusted public cloud platforms like Microsoft Azure—commonly integrated into legitimate IT operations—the threat actors could disguise their malicious activities as legitimate traffic, making it harder for security systems to detect their actions. This tactic also allowed them to bypass firewall restrictions and evade closer scrutiny.
“The campaign underscores the strategic nature of this threat, as breaching organizations that provide data, infrastructure, and cybersecurity solutions to other industries gives the attackers a foothold in the digital supply chain, enabling them to extend their reach to downstream entities.” concludes the report.
“The abuse of Visual Studio Code Remote Tunnels in this campaign illustrates how Chinese APT groups often rely on practical, solution-oriented approaches to evade detection. By leveraging a trusted development tool and infrastructure, the threat actors aimed to disguise their malicious activities as legitimate. The exploitation of widely used technologies, which security teams may not scrutinize closely, presents a growing challenge for organizations.”
“The Digital Eye operation highlights an increasing sophistication in the tactics of China-linked APT threats. The campaign demonstrates how traditional techniques, such as the use of SQLmap, can be combined with more innovative strategies, including the abuse of Visual Studio Code Remote Tunnels for C2 control, to orchestrate complex and hard-to-detect attacks.” Luigi Martire told Security Affairs. “Moreover, new malware artifacts, such as the PHPsert web shell and mimCN, have been identified, enabling attackers to operate almost invisibly to detection systems due to the lack of specific rules to identify them. This represents a significant risk for companies, even those with a relatively strong security baseline.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Operation Digital)
如有侵权请联系:admin#unsafe.sh