2023-12-20 19:48:15 Author: securityaffairs.com(查看原文) 阅读量:11 收藏
Sophisticated JaskaGO info stealer targets macOS and Windows
Pierluigi Paganini
December 20, 2023

JaskaGO is a new Go-based information stealer malware that targets both Windows and Apple macOS systems, experts warn.
Researchers from AT&T Alien Labs uncovered a previously undetected Go-based information stealer dubbed JaskaGO that targets Windows and macOS systems.
JaskaGO is a sophisticated malware that supports an extensive array of commands and can maintain persistence in different ways.
The macOS variant of the malware was first spotted in July 2023, it was spreading in the form of installers for pirated legitimate software such as CapCut or AnyConnect.
Following the discovery, researchers observed dozens of new samples that show the malware. The researchers pointed out that the recent malware sample still has a low detection rate.
Upon initial execution, the malware displays a fake error message, claiming a missing file, in an attempt to mislead the user into believing that the malicious code failed to run.
The malware also performs a series of checks to avoid execution in a virtualized environment.
“The malware conducts thorough checks to determine if it is operating within a virtual machine (VM). This process begins with the examination of general machine information, where specific criteria such as the number of processors, system up-time, available system memory, and MAC addresses are checked.” reads the report published by AT&T Alien Labs. “The presence of MAC addresses associated with well-known VM software, such as VMware or VirtualBox, is a key indicator.”
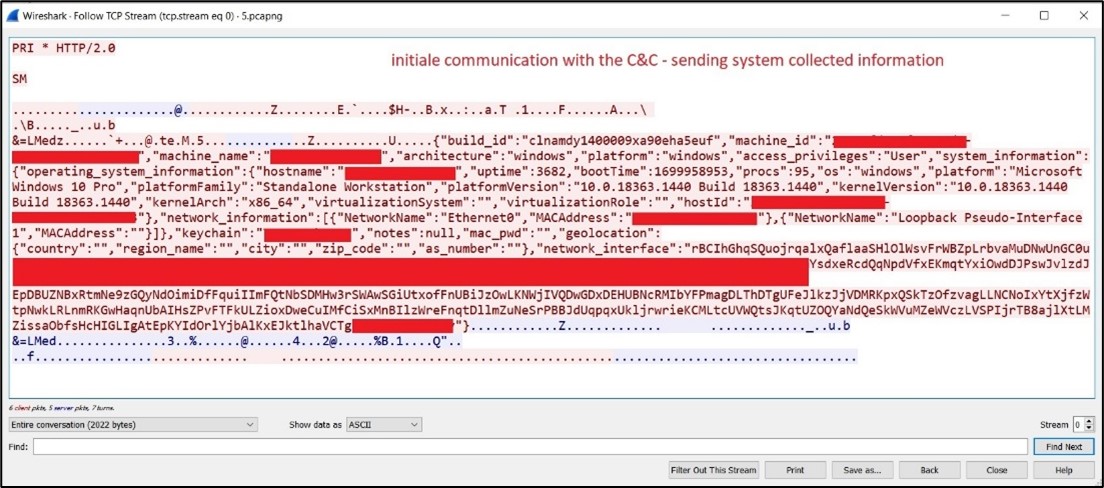
JaskaGO collects information from the infected system and connects to the C2 infrastructure awaiting for instructions.
The malware supports the following commands:
- Creating persistence for the malware (details in the subsequent section).
- Stealer functionalities: collecting information from the infected device and transmitting it to the command and control server.
- Pinging the command and control.
- Executing shell commands.
- Displaying alert messages.
- Retrieving running process list.
- Executing files on disk or in memory.
- Writing to the clipboard:a common tactic for stealing cryptocurrency funds.
- Performing a random task (like those in the VM detection section).
- Downloading and executing additional payloads.
- Initiating the process to exit (self).
- Initiating the process to exit and delete itself.

JaskaGO supports multiple exfiltration capabilities. The malware stores harvested data in a specially created folder, zipping and sending it to the C2.
The malware can steal the following info from Chrome and Firefox browsers:
- Browser credentials.
- History.
- Cookies: Files and folders – “Cookies”, “cookies.sqlite”, Network”.
- Password encryption keys key4.db – Stores the master key to decrypt all passwords stored in logins.json.
- Profile files (profile.ini, ^Profile\d+$).
- Login information – “Login Data” folder.
The info stealer also targets browser crypto wallet extensions and can exfiltrate files and folders.
On macOS, JaskaGO replies on a multi-step process to maintain persistence. It executes as Root, disables Gatekeeper, and duplicates itself, adopting the name format “com.%s.appbackgroundservice,” to obfuscate its presence on the system. The malware also creates a LaunchDaemon / LaunchAgent to ensure persistence.
“Employing sophisticated anti-VM tactics, JaskaGO sidesteps automatic analysis, making it a formidable challenge for detection. Its persistence mechanisms reveal a determined effort to embed itself within systems, while its stealer capabilities transform the malware into a dangerous threat, extracting sensitive information from unsuspecting victims.” concludes the report that includes indicators of compromise (IOCs).
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, JaskaGO)
如有侵权请联系:admin#unsafe.sh