2023-12-16 08:43:33 Author: securityaffairs.com(查看原文) 阅读量:14 收藏
New NKAbuse malware abuses NKN decentralized P2P network protocol
Pierluigi Paganini
December 16, 2023

Experts uncovered a new Go-based multi-platform malware, tracked as NKAbuse, which is the first malware abusing NKN technology.
Researchers from Kaspersky’s Global Emergency Response Team (GERT) and GReAT uncovered a new multiplatform malware dubbed NKAbuse. The malicious code is written in Go language, it is the first malware that relies on the NKN technology for data exchange between peers. The malicious code can target various architectures, it supports both flooder and backdoor capabilities.
The primary target of NKAbuse is Linux desktops, however, it can target MISP and ARM architecture.
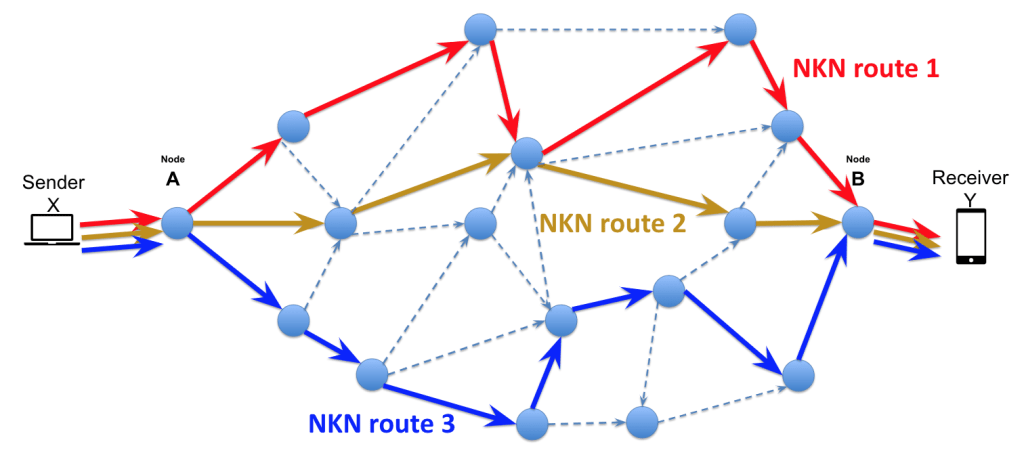
NKN (New Kind of Network) is a decentralized peer-to-peer network protocol that relies on blockchain technology. The protocol enables secure and low-cost data transfer. It is designed to address the limitations of current Internet infrastructure, which is centralized, inefficient, and vulnerable to censorship.

Individuals can voluntarily join the NKN network and run their nodes; it is currently composed of more than 60,000 nodes
“Historically, malware operators have exploited new and emerging communication protocols like NKN to link up with their command-and-control servers (C2) or bot masters.” reads the report published by Kaspersky. “This threat (ab)uses the NKN public blockchain protocol to carry out a large set of flooding attacks and act as a backdoor inside Linux systems.”
The experts believe threat actors exploited an old Struts2 vulnerability, tracked as CVE-2017-5638, while targeting a financial company.
The attackers exploited the vulnerability to execute commands on the server by passing them in a header labeled as ‘shell’ and transmitting the instructions to Bash for execution. Once exploited, a command is executed on the system to download the initial script.
The researchers noticed that the malware lacks of self-propagation mechanism, which means the initial infection vector is delivered by exploiting a vulnerability to deploy the sample.
The attackers usually install the malware by executing a remote shell script that downloads and executes the contents of the setup.sh shell script hosted a remote server. The malicious code checks the OS type to determine the second-stage malware (“app_linux_{ARCH}”), which is the actual malware implant, that is hosted on the same server. The sample discovered by Kaspersky supports the following architectures:
- 386
- arm64
- arm
- amd64
- mips
- mipsel
- mips64
- mips64el
NKAbuse maintains persistence by using cron jobs.
The malware supports multiple Distributed Denial of Service (DDoS) attacks, below is a list of the flooding payloads:
| Command | Attack |
| Default/0 | http_flood_HTTPGetFloodPayload |
| 1 | http_flood_HTTPPostFloodPayload |
| 2 | tcp_flood_TCPFloodPayload |
| 3 | udp_flood_UDPFloodPayload |
| 4 | ping_flood_PINGFloodPayload |
| 5 | tcp_syn_flood_TCPSynFloodPayload |
| 6 | ssl_flood_SSLFloodPayload |
| 7 | http_slowloris_HTTPSlowlorisPayload |
| 8 | http_slow_body_HTTPSlowBodyPayload |
| 9 | http_slow_read_HTTPSlowReadPayload |
| 10 | icmp_flood_ICMPFloodPayload |
| 11 | dns_nxdomain_DNSNXDOMAINPayload |
NKAbuse also supports multiple backdoor features that turn it into powerful remote access trojan (RAT),
“Although relatively rare, new cross-platform flooders and backdoors like NKAbuse stand out through their utilization of less common communication protocols. This particular implant appears to have been meticulously crafted for integration into a botnet, yet it can adapt to functioning as a backdoor in a specific host.” concludes the report. “Moreover, its use of blockchain technology ensures both reliability and anonymity, which indicates the potential for this botnet to expand steadily over time, seemingly devoid of an identifiable central controller.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, ransomware)
如有侵权请联系:admin#unsafe.sh