2023-12-9 23:49:44 Author: securityaffairs.com(查看原文) 阅读量:12 收藏
5Ghoul flaws impact hundreds of 5G devices with Qualcomm, MediaTek chips
Pierluigi Paganini
December 09, 2023

A set of flaws, collectively called 5Ghoul, in the firmware implementation of 5G mobile network modems from major vendors impacts Android and iOS devices.
A team of researchers from the Singapore University of Technology and Design discovered a set of security vulnerabilities in the firmware implementation of 5G mobile network modems from major chipset vendors. The flaws impact prominent vendors, including MediaTek and Qualcomm.
The researchers noticed that numerous 5G commercial products, such as smartphones, CPE routers, and USB modems, may be impacted. The vulnerabilities affect 5G modems, 10 issues impacts Qualcomm and MediaTek, and three of them are rated high severity.
“In this vulnerability disclosure report, we discuss details of 5Ghoul – a family of implementation-level 5G vulnerabilities. Such a family of vulnerabilities are present in the firmware implementation of 5G mobile network modems from major chipset vendors i.e., Qualcomm and MediaTek.” reads the report. “As of today, we disclose a total of 14 vulnerabilities (10 CVEs), of which 10 affect commercial off-the-shelf (COTS) edge devices employing 5G modems from Qualcomm and MediaTek. At least two other vulnerabilities are not disclosed yet due to confidentiality.”
Threat actors can exploit the vulnerabilities to block connections, freeze connections that force the manual reboot or downgrade the 5G connectivity to 4G.
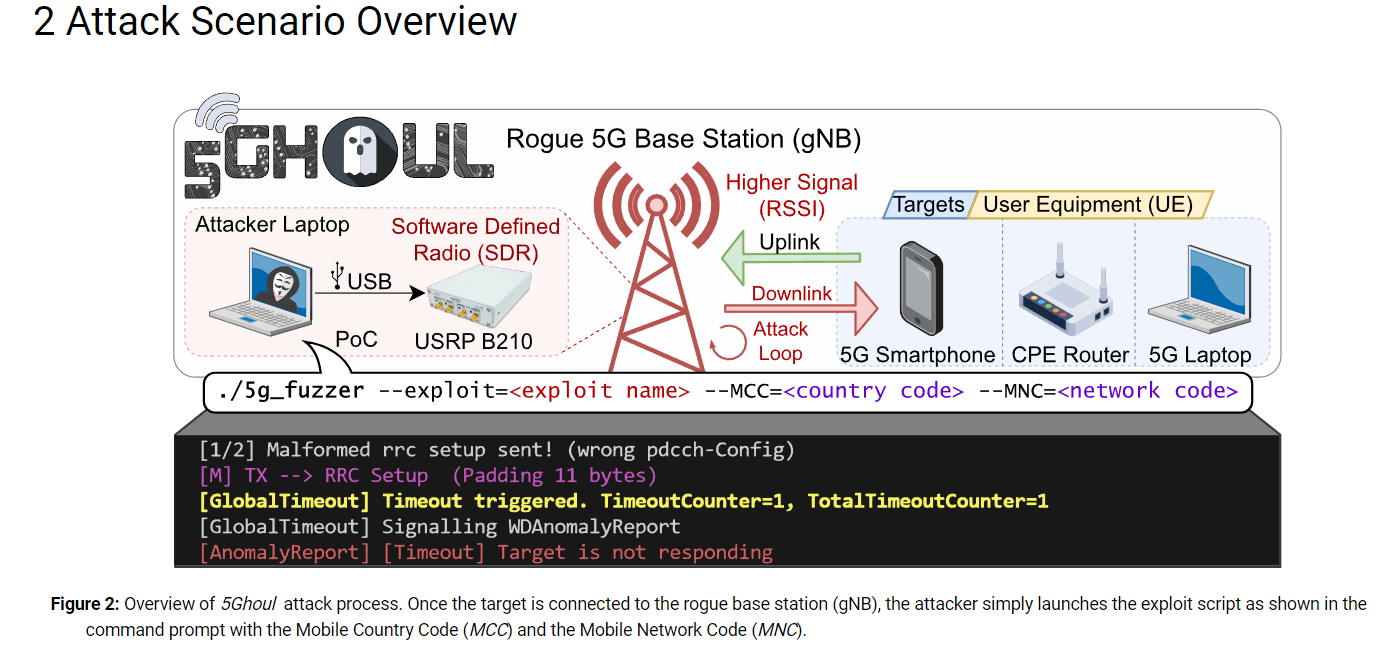
The 5Ghoul attacks rely on a model that mimics a limited Dolev-Yao adversary, the attackers attempt to deceive a 5G-enabled target device to connect a rogue base station (gNB). This is achieved by revealing an Adversary-Controlled Downlink channel, enabling the injection and modification of 5G NR Downlink Packets from an actual 5G stack implementation using OpenAirInterface (gNB) and Open5GS (5G Core Network).
This is accomplished by exposing an Adversary-Controlled Downlink channel that can arbitrarily inject and/or modify 5G NR Downlink Packets generated from a real 5G stack implementation based on OpenAirInterface (gNB) and Open5GS (5G Core Network).
The attackers have to impersonate the legitimate gNB using the known Cell Tower connection parameters (e.g., SSB ARFCN, Tracking Area Code, Physical Cell ID, Point A Frequency). Free software like Cellular-Pro allows it.
The researchers pointed out that the attacker does not need to be aware of any secret information of the target UE, such as UE’s SIM card details, to complete the NAS network registration.
The attacker must be sufficiently close to the target UE and the Received Signal Strength Indicator (RSSI) of the adversarial gNB is higher than the legitimate gNB. The target device will connect to the adversarial gNB. The adversarial gNB can freely manipulate downlink messages to the target UE throughout the message exchanges.

“In practicality, 5Ghoul vulnerabilities can be easily exploited over-the-air by starting a malicious gNB within radio range of the target 5G UE device.” continues the report. “This is a practical setup which relies on using Software Defined Radio (SDR) to behave as a cloned gNB. While USRP B210 used in our setup could be recognized from afar, thus making the attack visually noticeable, such type of equipment has already been miniaturized to the size of a Raspberry Pi. This, in turn, enables the use of SDR for visibly stealthy attacks.”
The vulnerabilities impact 714 smartphones from 24 vendors, including Samsung, OnePlus, Oppo, Vivo, Xiaomi, Apple, and Google.
Below is the list of vulnerable targets used in the tests by the researchers and their firmware versions:

The following table includes the list of 5G implementation vulnerabilities and affected software or products:
At the time of publishing the report, both MediaTek and Qualcomm have already released security updates to address 12 of the 14 vulnerabilities. The patches for the other two flaws are expected to be disclosed in the future.
“While 5G comes with a lot of potential for supporting complex applications, we foresee the need for deeper research in automatically and comprehensively hunting for implementation-level vulnerabilities in 5G software systems.” concludes the report. “Considering the multi-layer, complex implementation of 5G network stack and its closed nature, the research in 5G security testing has a long way ahead. This is evident from the discovery of 5Ghoul vulnerabilities in major chipset vendors, who, despite having all the resources for comprehensively testing their own 5G stack, are still susceptible to 5Ghoul vulnerabilities.“
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, 5Ghoul vulnerabilities)
如有侵权请联系:admin#unsafe.sh
