2023-10-25 21:8:53 Author: www.horizon3.ai(查看原文) 阅读量:24 收藏
Summary
Mirth Connect, by NextGen HealthCare, is an open source data integration platform widely used by healthcare companies. Versions prior to 4.4.1 are vulnerable to an unauthenticated remote code execution vulnerability, CVE-2023-43208. If you’re a user of Mirth Connect, you’ll want to upgrade to the latest patch release, 4.4.1, as of this writing.
Background
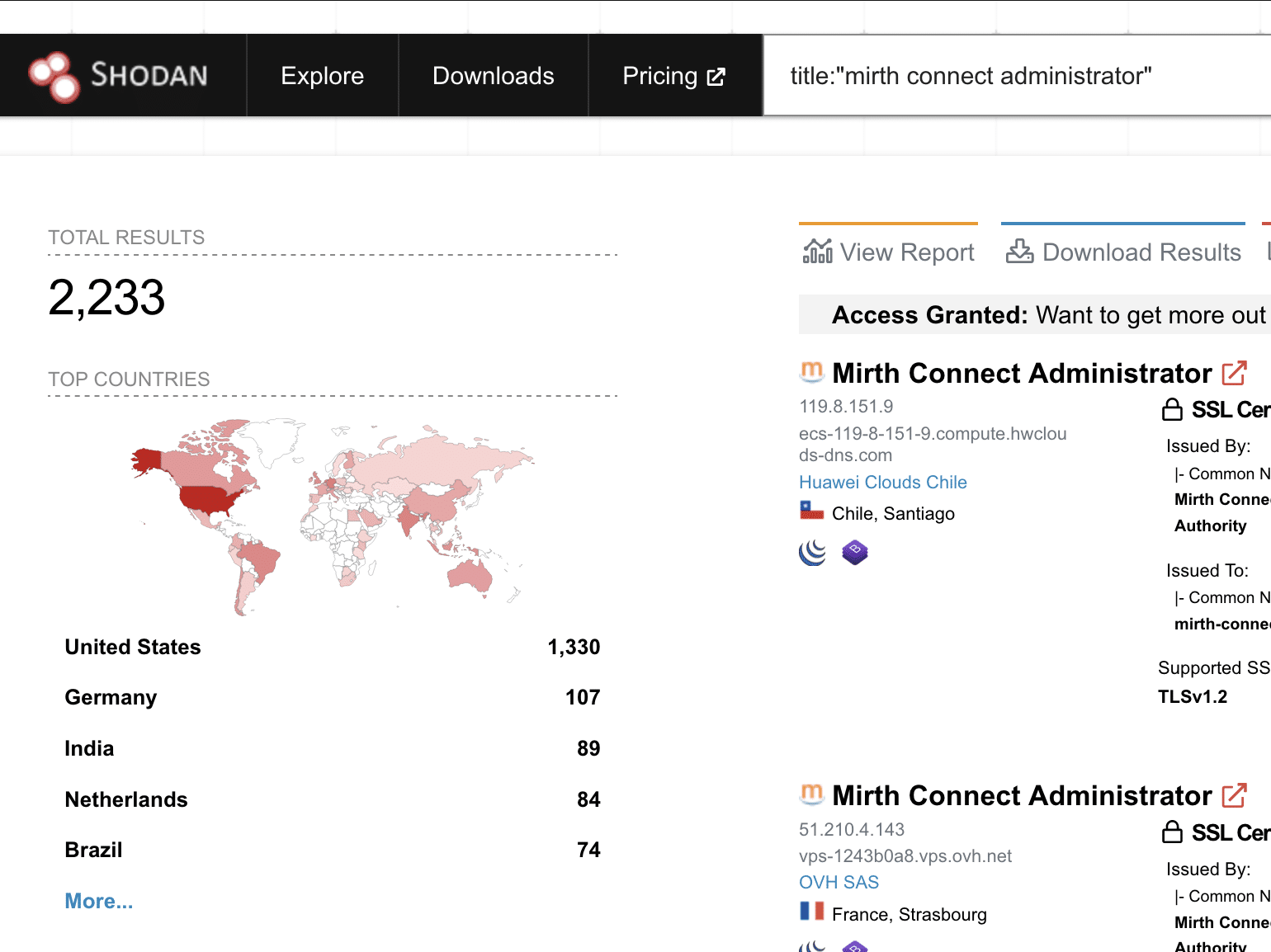
A few months ago, we came across an unauthenticated remote code execution vulnerability, CVE-2023-37679, affecting Mirth Connect that was reported by IHTeam. Mirth Connect is an interesting application for us at Horizon3 because a number of our clients are in the healthcare space and use this application. Healthcare companies are commonly targeted by ransomware threat actors, and this application has decent exposure on the Internet (about 1200+ unique hosts).
CVE-2023-37679 was reported to be fixed in Mirth Connect 4.4.0. In the release notes for 4.4.0, it was reported as only affecting Mirth Connect installs running on Java 8 or below. This caught our attention (why only Java 8?), and we started digging. We found that in fact, all installs of Mirth Connect, regardless of the Java version, were vulnerable. We also found that the patch for CVE-2023-37679 could be bypassed. We subsequently reported a new vulnerability to NextGen, tracked as CVE-2023-43208. The fix for CVE-2023-43208 is in 4.4.1.
Impact
This is an easily exploitable, unauthenticated remote code execution vulnerability. Attackers would most likely exploit this vulnerability for initial access or to compromise sensitive healthcare data.
We are not releasing an exploit at this time, but the methods for exploitation (involving Java XStream) are well known and documented. We have verified that Mirth Connect versions going as far back as 2015/2016 are vulnerable.
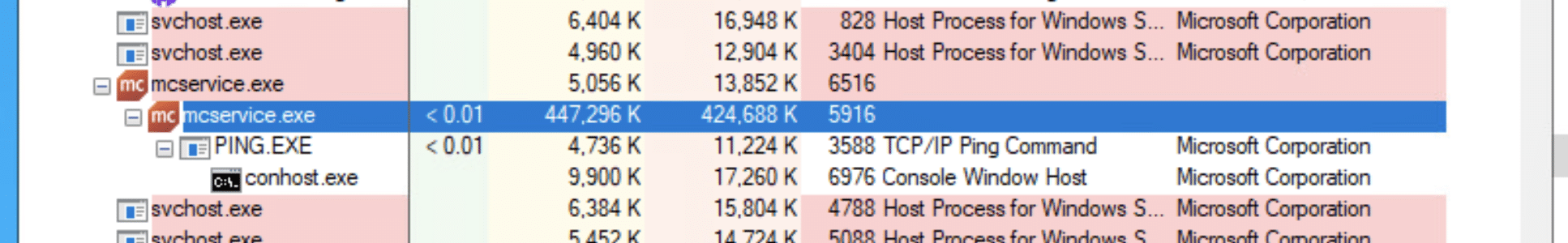
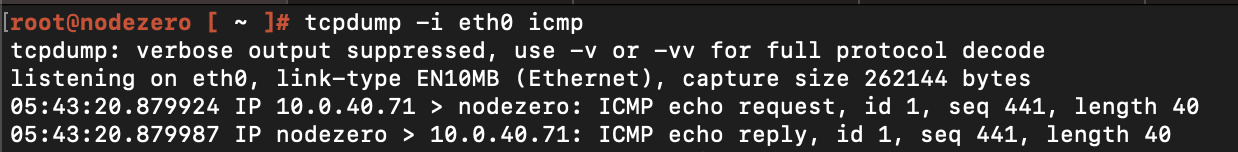
On Windows systems, where Mirth Connect appears to be most commonly deployed, it typically runs as the SYSTEM user. Here’s an example of exploiting this vulnerability to run the ping command on a Windows host:
Detection
The version of the Mirth Connect server can be determined as follows:
% curl -k -H 'X-Requested-With: OpenAPI' https://<server>:<port>/api/server/version
4.4.0
Any server reporting a version less than 4.4.1 is highly likely to be exploitable.
Remediation
We urge all users of Mirth Connect, especially instances that are Internet-facing, to prioritize updating to 4.4.1 ASAP.
Timeline
- Sept. 8, 2023: Horizon3 sends initial report to NextGen
- Sept. 8, 2023: NextGen acknowledges receipt
- Oct. 6, 2023: NextGen provides Horizon3 a test build for 4.4.1
- Oct. 13, 2023: Horizon3 completes testing/review of test build
- Oct. 17, 2023: NextGen releases 4.4.1
- Oct. 25, 2023: This post
We’d like to thank NextGen for the prompt handling of this vulnerability, and a hat tip to IHTeam for discovering the original issue.
References
如有侵权请联系:admin#unsafe.sh