嗯,用户让我帮忙总结一篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”或者“这篇文章”这样的开头,直接写描述即可。首先,我需要仔细阅读用户提供的文章内容,理解其主要信息。 文章主要讲的是Citizen Lab报告中提到的Webloc工具被全球执法机构用来追踪设备。这个工具通过广告数据追踪了多达5亿台设备。开发者是Cobwebs Technologies,现在由Penlink销售。它被美国、匈牙利和萨尔瓦多的执法机构使用,涉及军方、情报机构和多个警察部门。 接下来,我需要提取关键信息:Webloc工具、广告数据追踪、5亿设备、执法机构使用、涉及国家和地区、隐私和法律问题。然后,把这些信息浓缩成一句话,不超过100字。 可能的结构是:Citizen Lab报告指出Webloc工具利用广告数据追踪5亿设备,被多国执法机构用于监控,引发隐私和法律争议。 这样既涵盖了主要点,又简洁明了。确保没有使用任何开头词,直接进入描述。 </think> Citizen Lab报告指出Webloc工具利用广告数据追踪5亿设备,被多国执法机构用于监控,引发隐私和法律争议。 2026-4-13 10:44:33 Author: securityaffairs.com(查看原文) 阅读量:20 收藏
Citizen Lab: Webloc tracked 500M devices for global law enforcement

Citizen Lab reported that law enforcement used the surveillance tool Webloc to track up to 500M devices via ad data globally.
A report by Citizen Lab revealed that law enforcement agencies in the U.S., Hungary, and El Salvador used a surveillance tool called Webloc to track devices via advertising data, potentially affecting up to 500 million devices. Developed by Cobwebs Technologies and now sold by Penlink, the tool is widely used by agencies like ICE, the military, and multiple police departments.
Cobwebs Technologies has links to spyware vendor Quadream through its founder. Its Webloc tool is sold alongside the Tangles intelligence platform and is used globally by law enforcement.
“Our research shows that intrusive and legally questionable ad-based surveillance (i.e. without a warrant or adequate oversight) is being used by military, intelligence, and law enforcement agencies down to local police units in several countries across the globe.” reads the report published by Citizen Lab.
Citizen Lab found that the Webloc surveillance tool is used by governments in Hungary, El Salvador, and the United States, marking the first confirmed use of ad-based tracking in Europe. The tool is also linked to multiple law enforcement agencies and possibly other countries.
Despite limited transparency from European authorities, evidence suggests broader global use.
Ad-based surveillance emerged after a 2020 investigation revealed U.S. agencies buying smartphone location data from apps via brokers. Since then, multiple government bodies have used this data for surveillance purposes.
Using advertising data sources, it tracks devices via mobile advertising IDs, linking them to GPS, Wi-Fi, and behavioral data such as apps used, interests, and demographics. It supports geofencing, travel tracking, and relationship mapping between devices, enabling large-scale surveillance.

The data allowed intelligence and law enforcement to cover behavior, traits, and movements of millions. Known as ADINT, it relies on data from ad auctions (RTB) and embedded app trackers (SDKs), collecting identifiers, geolocation, and user habits. Despite claims of anonymity, such data can identify individuals. This practice enables large-scale tracking but raises serious privacy and legal concerns, as it may expose sensitive personal details and bypass traditional oversight.
Webloc offers both historical and near real-time geolocation data, with updates occurring every 4 to 24 hours and access to up to three years of past records. The platform processes extensive personal data, including device identifiers (e.g., advertising IDs, IPs), timestamps, GPS and Wi-Fi-based locations, inferred places like home or work, device details, and behavioral profiles derived from ad-targeting segments. It can also track apps used and user characteristics such as age, gender, and interests. Although vendors claim GDPR compliance and user consent, such assertions remain disputed. Even without explicit demographic data, location traces can reveal highly sensitive insights about individuals’ habits and identities. The exact data sources remain unclear but likely include SDK- and RTB-based pipelines. Coverage, accuracy, and current practices are difficult to verify.
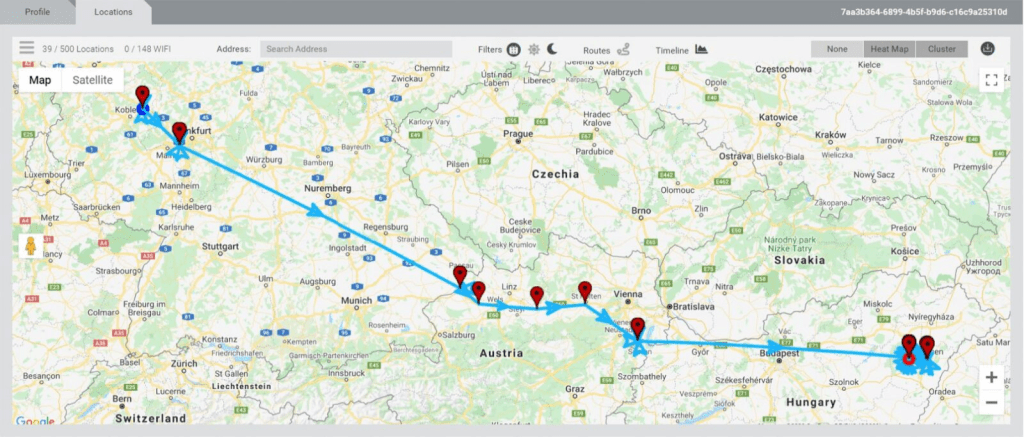
Researchers uncovered additional infrastructure linked to Cobwebs by pivoting on TLS certificates, identifying 14 new servers, some exposing broken login pages tied to products like Trapdoor and Weaver. Overall, 219 active servers were assessed as likely supporting Cobwebs deployments, with a broader infrastructure of 298 servers across 25 countries, heavily concentrated in the U.S., Netherlands, and Germany.
“Based on the above research, we identified 219 active servers we assess as associated with Cobwebs product deployments. With the help of common IP geolocation tools we then retrieved the likely server locations of the corresponding IP addresses.” continues the report. “As a result, we found that many potential Cobwebs product servers are located in the U.S. (126), Netherlands (32), Singapore (17), Germany (8), Hong Kong (8), and the U.K. (7). We also identified potential product servers located in Kenya, Iraq, United Arab Emirates, Indonesia, India, Mexico, Colombia, Australia, Japan, and in several European countries (France, Sweden, Norway, Ireland, and Cyprus). We found only one potential product server located in Cobwebs Technologies’ home country, Israel.”
Most are hosted on Microsoft Azure. Evidence suggests dynamic infrastructure, with some servers active only briefly and others persisting for years.
Analysis also points to specialized deployments such as “Webloc” and “Trapdoor,” inferred from hostname patterns (e.g., “wl” and “td”). Trapdoor, in particular, emerges as a web-based social engineering platform capable of phishing, data extraction, and limited client-side interaction via browsers, potentially facilitating malware delivery without embedding it directly.
Corporate links connect Cobwebs to other surveillance vendors like Quadream, with overlapping leadership and investment networks. Despite vendor claims of compliance, the report highlights significant opacity around operations, customers, and legal safeguards. It ultimately characterizes Webloc as a highly intrusive mass surveillance system leveraging commercial data, raising serious concerns about proportionality, legality, and civil liberties.
Cobwebs Technologies and its successor Penlink provide limited transparency about Webloc, a mass surveillance platform leveraging data from mobile apps and digital advertising. The system enables large-scale monitoring of individuals’ movements and behaviors, often without probable cause, raising significant privacy concerns. Its use illustrates “mission creep,” expanding from serious investigations to routine cases. The legality of such surveillance is widely debated, especially regarding consent and data anonymization. Regulatory scrutiny in the U.S. and Europe highlights potential violations of privacy laws. The report urges stronger oversight, reforms in data practices, and further investigation into Webloc’s data sources, usage, and impact on civil liberties.
“The systematic misuse of data purchased from everyday consumer apps and digital advertising for warrantless surveillance raises serious concerns about civil liberties and fundamental rights, particularly when used to target vulnerable groups such as immigrants or those who exercise their freedom of expression and assembly rights.” concludes the report. “Ad-based surveillance raises specific concerns when applied by organizations or governments, which are prone to authoritarianism or have weak or limited oversight. It generally raises concerns when governments lack a lawful basis to use it or when the underlying data is processed without a lawful basis.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Webloc)
如有侵权请联系:admin#unsafe.sh