好的,用户让我总结一篇关于Censys发现5219个暴露设备的文章,控制在100字以内。首先,我需要通读文章,抓住关键信息。 文章提到Censys研究人员发现了5219个Rockwell PLC设备暴露在互联网上,大部分在美国。这些设备容易受到伊朗APT组织的攻击。威胁行为者利用这些暴露的设备进行网络攻击,目标是关键基础设施,如政府服务、水务系统和能源部门。 攻击手段包括篡改项目文件和SCADA系统数据,导致运营中断和财务损失。当局建议组织审查妥协指标,并采取缓解措施。Censys指出这些设备分布在美国、西班牙、台湾等地,很多通过蜂窝网络连接,增加了监控和补丁的难度。 总结时要涵盖主要发现:设备数量、地理位置、威胁来源、攻击影响以及建议措施。控制在100字以内,直接描述内容,不使用开头语。 现在组织语言:Censys发现5219个Rockwell PLC设备暴露在线,主要在美国。这些设备易受伊朗APT攻击,影响关键基础设施如能源和水务。研究人员建议断开或加强安全措施。 </think> Censys发现5,219个Rockwell PLC设备暴露在线,主要位于美国。这些设备易受伊朗APT攻击,影响关键基础设施如能源和水务。研究人员建议断开或加强安全措施以降低风险。 2026-4-11 20:39:37 Author: securityaffairs.com(查看原文) 阅读量:21 收藏
Censys finds 5,219 devices exposed to attacks by Iranian APTs, majority in U.S.

Censys researchers found 5,219 exposed Rockwell PLCs online, mostly in the U.S., urging defenders to secure or disconnect them.
On April 7, 2026, U.S. agencies, including FBI, CISA, and NSA, warned of Iran-linked APTs exploiting internet-exposed Rockwell Automation PLCs.
Threat actors are carrying out cyberattacks targeting internet-connected operational technology (OT) across multiple critical infrastructure sectors. Iran-linked actors are believed to be behind the activity, aiming to cause disruption in areas such as government services, water systems, and energy.
The attacks involve manipulating project files and altering data shown on HMI and SCADA systems, leading in some cases to operational disruptions and financial losses. Authorities urged organizations to review indicators of compromise and apply mitigations to reduce risks. The campaign has been linked to groups like CyberAv3ngers, associated with Iran’s IRGC.
Organizations are advised to assess exposed devices, follow security guidance from vendors, disconnect systems from the internet where possible, and coordinate with authorities for incident response and mitigation support.
Censys researchers identified 5,219 exposed devices globally, 74.6% in the U.S., many on cellular networks. Analysis of indicators suggests multiple IPs tied to a single compromised engineering workstation, expanding the known attack surface beyond initial disclosures.
“Censys identifies 5,219 internet-exposed hosts globally responding to EtherNet/IP (port 44818) and self-identifying as Rockwell Automation/Allen-Bradley devices.” reads the report published by Censys. “Geographic distribution is heavily skewed toward the United States, which accounts for 74.6% of global exposure — consistent with Rockwell’s dominant market position in North American industrial automation.”

The researchers pointed out that the exposure of Rockwell Automation PLCs extends beyond the U.S., with notable concentrations in Spain, Taiwan, and Italy, while Iceland shows disproportionate exposure. According to Censys, many devices are connected via cellular networks, with providers like Verizon and AT&T accounting for a large share. This indicates field-deployed systems (e.g., utilities and substations) relying on cellular or even satellite links like Starlink, making monitoring and patching difficult.
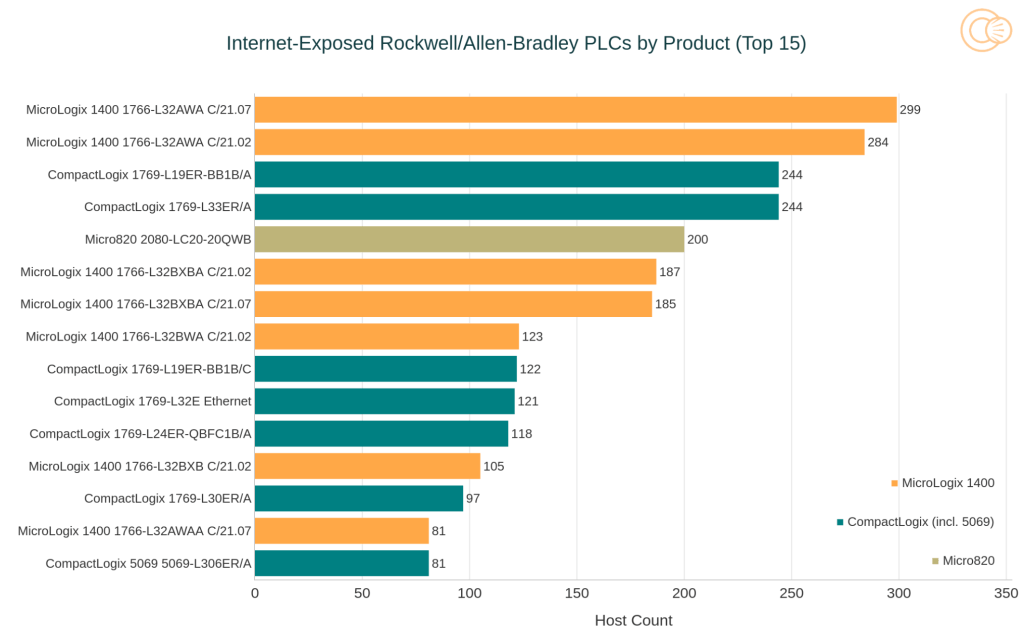
Most exposed devices belong to MicroLogix and CompactLogix families, often running outdated firmware.
“EtherNet/IP identity responses expose device-level product strings, enabling granular fingerprinting of PLC model and firmware revision without authentication.” continyes the report. “The top 15 product strings are dominated by two families: MicroLogix 1400 (catalog prefix 1766-) and CompactLogix (1769-, 5069-), with one Micro820 (2080-) entry.”

Since device details can be identified remotely without authentication, attackers can easily scan, identify, and prioritize vulnerable systems, increasing risks for sectors like energy and water infrastructure.
Censys found that 5,219 exposed Rockwell Automation PLC hosts often run extra services beyond EtherNet/IP, increasing risk. Key exposures include VNC for remote HMI access, Telnet (cleartext legacy access), Modbus for OT communication, and Red Lion Crimson in mixed-vendor setups. These services expand attack paths and raise the risk to industrial systems.
The report also provides Indicators of Compromise (IOCs) and technical details about the operator infrastructure.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Rockwell PLCs)
如有侵权请联系:admin#unsafe.sh