嗯,用户让我总结一篇文章,控制在100字以内,而且不需要特定的开头。我得先仔细阅读文章内容,抓住关键点。 文章讲的是Masjesu这个僵尸网络,它从2023年开始活跃,专门针对物联网设备,比如路由器和网关。它通过DDoS-for-hire服务来运作,广告是在Telegram上发布的。这个僵尸网络设计得很隐蔽,避免攻击高知名度的网络,比如美国国防部的IP地址,这样不容易被发现。 此外,Masjesu使用多阶段XOR加密来隐藏恶意代码和配置,防止被静态检测发现。它还会扫描随机IP,并利用已知漏洞传播。它的C2服务器使用多个域名和备用IP,确保即使部分被封也能继续运行。 总结下来,Masjesu是一个针对多种架构物联网设备的DDoS僵尸网络,隐蔽性强,设计用于长期生存和低风险攻击。 </think> Masjesu 是一个针对 IoT 设备的 DDoS 僵尸网络,自 2023 年起活跃并隐藏运行。它通过 Telegram 广告出租服务,攻击路由器等设备并避免高风险网络以长期存活。 2026-4-9 14:6:34 Author: securityaffairs.com(查看原文) 阅读量:13 收藏
Masjesu botnet targets IoT devices while evading high-profile networks

Masjesu is a stealthy DDoS-for-hire botnet targeting IoT devices, active since 2023 and designed to stay hidden by avoiding high-profile networks.
Masjesu is a stealthy botnet active since 2023, advertised as a DDoS-for-hire service. It targets IoT devices like routers and gateways, spanning multiple architectures. Designed for persistence, it executes carefully, avoiding high-profile IP ranges such as the U.S. Department of Defense to remain undetected and survive long-term, favoring low-key attacks over mass infection.
“The Masjesu botnet, a sophisticated, commercially-run Internet of Things (IoT) threat, has been operational and evolving since early 2023, continuing into 2026. Its primary focus is stealth, and it is offered as a “Distributed Denial of Service (DDoS)-for-hire service,” typically marketed via Telegram. It targets a wide array of IoT devices, such as routers and gateways, across multiple architectures (including i386, MIPS, ARM, and AMD64).” reads the report published by Trellix. “Built for persistence and low visibility, Masjesu favors careful, low-key execution over widespread infection, deliberately avoiding blocklisted IP ranges such as those belonging to the Department of Defense (DoD) to ensure long-term survival.”
Masjesu hides its strings, configs, and payloads with XOR encryption to bypass static detection. It scans random IPs and exploits vulnerabilities in devices from D-Link, GPON, and Netgear to spread. Its C2 setup uses multiple domains and fallback IPs and runs TCP, UDP, and HTTP flood attacks.

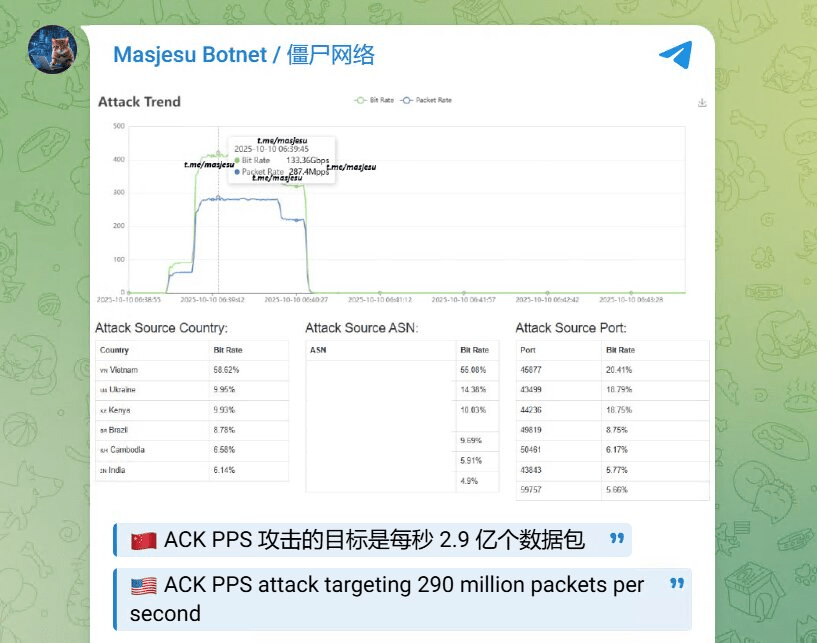
The botnet targets IoT devices across multiple architectures like i386, MIPS, ARM, SPARC, PPC, 68K, and AMD64, hitting routers, gateways, and embedded systems. Operators advertise on Telegram. The original channel with over 2,000 subscribers was banned; the new channel “Masjesu Botnet / 僵尸网络” has aroud 420 subscribers. Posts appear in English and Chinese, showing attacks and metrics.
Masjesu launched DDoS floods up to approximately 290 Gbps, drawing traffic from countries like Vietnam, Ukraine, Iran, Brazil, Kenya, and India, with Vietnam providing nearly half. Operators market its large, stable, and geographically diverse botnet to target CDNs, game servers, and enterprises.

The bot starts by binding to a fixed TCP port (55988) and hardens itself by ignoring termination signals. The malware hides critical data using multi-stage XOR encryption and decrypts it only at runtime, revealing C2 domains and system details.
To achieve persistence, the malware renames itself as a legitimate system file (e.g., /usr/lib/ld-unix.so.2), installs a cron job to run every 15 minutes, and daemonizes to operate silently. It also spoofs process names like systemd-journald to avoid detection.
Masjesu kills competing processes (wget, curl, sshd) and locks down /tmp to maintain exclusive control. Its C2 uses multiple domains with a fallback IP, retrieving commands and payloads via HTTP.
For propagation, the bot scans random IPs, avoids sensitive ranges (e.g., DoD), and exploits known flaws in routers and IoT devices (D-Link, GPON, Netgear, etc.).
“Masjesu utilizes the Createchildrenreplic() function for further propagation. This function scans random IP addresses,excluding a catalog of blocklisted IP address ranges (Table 2), for specific hardcoded open ports.” continues the report. “Based on the port identified, a corresponding vulnerability exploit is executed on the target device. Upon successful exploitation, the malicious payload is downloaded onto the compromised device.”
Once infected, bots execute DDoS attacks (TCP, UDP, HTTP floods) based on C2 instructions.
Overall, Masjesu combines obfuscation, resilience, and wide exploitation to sustain a distributed, hard-to-detect attack infrastructure.
“Masjesu (XorBot) is a rapidly maturing IoT botnet focused on DDoS-for-hire, primarily marketed via Telegram and resistant to takedowns. Technically, it minimizes detectability and maximizes attack effectiveness by randomizing packet headers and payloads to better mimic legitimate traffic.” concludes the report. “The botnet continues to expand by infecting a broad range of IoT devices across multiple architectures and manufacturers. “
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Masjesu botnet)
如有侵权请联系:admin#unsafe.sh