
好的,我需要帮用户总结一篇文章的内容,控制在100字以内,而且不需要特定的开头。首先,我得仔细阅读这篇文章,理解它的主要观点。 文章主要讨论了网络安全行业中的一个严重问题:安全运营中心(SOC)每天处理大量警报,但分析师数量不足,导致每个警报只能快速处理,无法进行深入分析。作者通过数学计算展示了这个问题的严重性。 接下来,我需要提取关键点:每天2000个警报,每个警报需要20分钟处理,但实际上分析师只能花6.7分钟处理每个警报。这导致大部分警报没有被充分审查,增加了被攻击的风险。 然后,文章提到解决方案是使用AI自主平台Morpheus来处理初步筛选,这样分析师可以专注于更有战略性的任务。最后,用户需要一个简短的总结,所以我要把这些要点浓缩到100字以内。 现在开始组织语言:描述问题、计算结果、解决方案和影响。确保语言简洁明了。 </think> 文章指出网络安全行业存在严重的人力缺口问题。 SOC每天需处理数千个警报,但分析师数量远不足以完成每条警报的深入分析。数据显示每条警报平均仅能分配6.7分钟处理时间,导致75%以上的警报未被充分审查。文章建议采用AI自主平台进行初步筛选以缓解这一困境。 2026-3-4 20:11:26 Author: securityboulevard.com(查看原文) 阅读量:6 收藏
Your analysts are gambling with alerts, and the math proves it.
The cybersecurity industry has quietly agreed to avoid doing one very simple calculation: dividing the number of daily alerts by the number of analysts available to work them, then comparing the result to the time actually required for a proper triage. When you run that math, the story it tells is uncomfortable. Every CISO needs to hear it.
The 20-minute standard nobody meets
Industry research consistently puts proper alert investigation at 20–40 minutes per alert. IDC puts it at 30 minutes for a false positive alone. IBM’s Cost of Data Breach research and Cybersecurity Insiders both land in the same range. Not a glance at the alert. Triage it. Normalize the data, correlate against threat intel, check asset criticality, examine user behavior baselines, and make an informed disposition decision.
For L2 escalations, add another 30–45 minutes on top of that.
These are the numbers the industry publishes, the numbers vendor ROI models assume, the numbers compliance frameworks implicitly require. So let’s use the conservative end: 20 minutes per L1 alert.
2,000 alerts. Do the math.
A mid-to-large enterprise SOC ingesting 2,000 alerts per day is not unusual. At 20 minutes per L1 triage, that’s 40,000 analyst-minutes of work, every single day. With each analyst delivering roughly 420 productive minutes per shift, you need 95 L1 FTEs just to keep up.
Add L2 investigation for the 30% that escalate (600 alerts × 40 minutes), and you need another 57 L2 FTEs.
That’s 152 analysts for triage and investigation alone, before shift leads, management, or engineering. At $120K fully burdened per head — a conservative US market figure — you’re looking at north of $18 million per year in analyst compensation.
The one-third reality
Most SOCs operate at roughly one-third of that headcount. Not because they’re negligent. The budget, the talent market, and a 3.4-million-person global cybersecurity workforce shortage make full staffing impossible.
At one-third staffing, your 32 L1 analysts each face 63 alerts per shift. Available time per alert: 6.7 minutes.
Six minutes and forty seconds. That’s what sits between your organization and the next breach.
In 6.7 minutes, an analyst can open the alert, scan the severity, glance at a log line or two, and make a gut call. What they cannot do is correlate with threat intelligence, assess lateral movement risk, examine user behavior anomalies, validate detection logic, or evaluate blast radius. Everything that constitutes real triage gets skipped.
The result? An estimated 1,500 alerts per day — 75% or more of your total volume — receive either a cursory rubber-stamp or no review at all.
The binary question
This forces an honest conclusion:
Option A: Your SOC has ~152 analyst FTEs and an $18M+ triage budget. You’re covered.
Option B: It doesn’t. Your alerts are not being properly triaged. Every ignored alert is a door an adversary could walk through undetected.
For the vast majority of organizations, the answer is B. Post-breach forensics confirm the pattern over and over: the detection tools fired. The alert sat in a queue. The analyst closed it in under a minute. The adversary moved laterally for weeks.
Why the usual fixes fail
Hiring more analysts runs into cost and talent scarcity simultaneously. Even organizations willing to pay cannot fill 100 open analyst requisitions in any reasonable timeframe.
Tuning alert volume down trades noise for blind spots. Every suppressed detection rule is an attack vector you’ve voluntarily stopped watching.
SOAR playbooks automate lookups and workflow, but they can’t reason. They execute deterministic rules. They don’t assess ambiguous signals, recognize novel attack chains, or weigh contextual risk.
MSSPs face the exact same math. The triage deficit is transferred, not solved.
AI-autonomous triage: what it actually looks like
The gap here is structural. You have more alerts than humans can process at the depth those alerts require. No amount of hiring, tuning, or outsourcing changes that ratio. You need a different model.
D3 Security’s Morpheus performs full-depth triage in 30–90 seconds per alert. It normalizes data across sources, correlates with threat intelligence, maps to MITRE ATT&CK, traces attack paths across your environment, assesses blast radius, and delivers a documented disposition with a complete evidence chain.
Every alert. All 2,000. Every day.
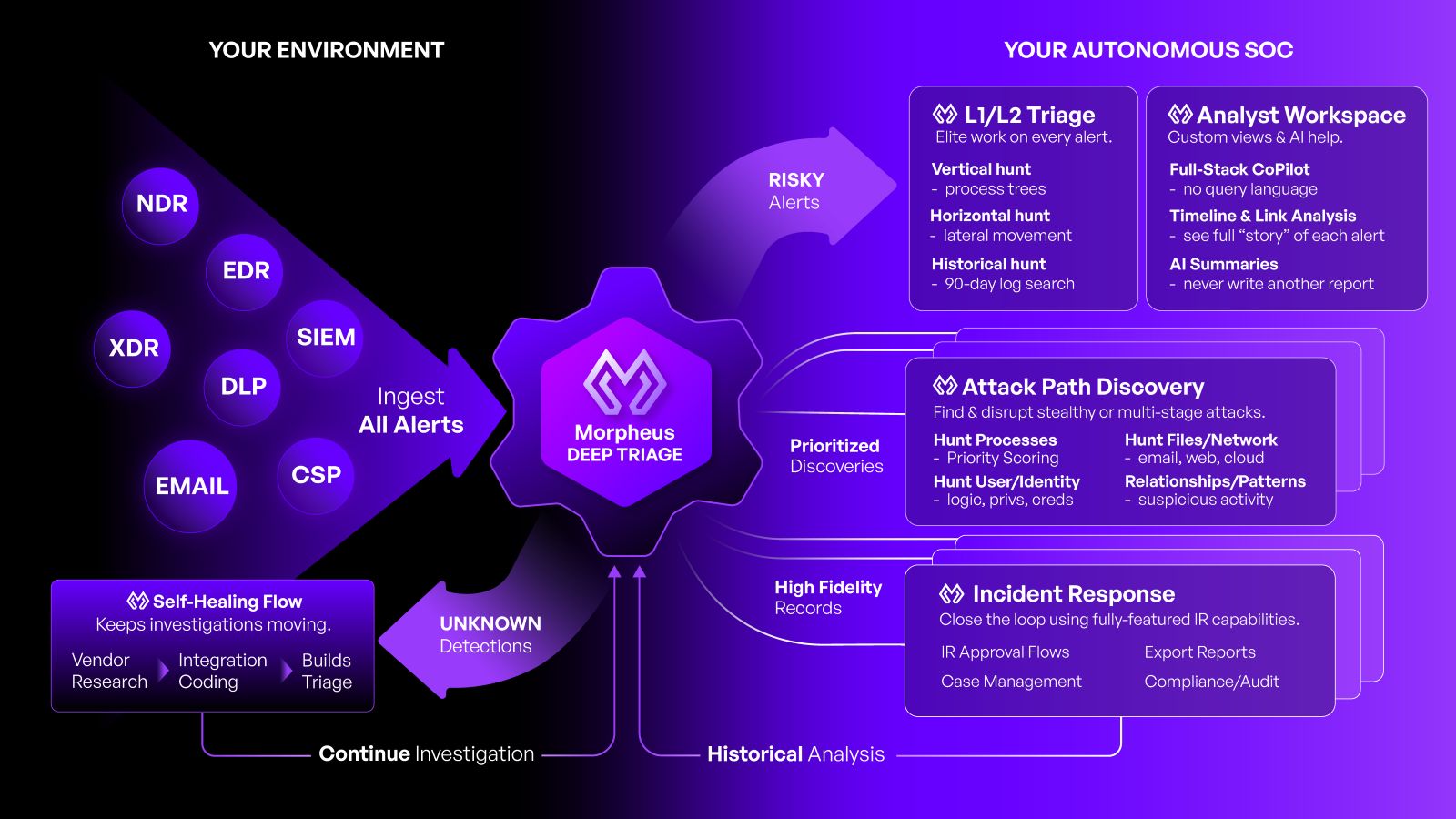
Where Morpheus goes further is Attack Path Discovery. Instead of treating each alert as an isolated event, it queries for correlated activity across reconnaissance, execution, persistence, lateral movement, and exfiltration stages. Think of it as the difference between checking a single alarm and figuring out whether someone is already inside the building.
What your analysts actually get to do
When AI handles first-line triage, your team stops drowning in queue management. They get time for threat hunting, incident response, detection engineering — the strategic work that actually reduces risk.
Burnout drops. Retention improves. And for the first time, you can tell your board, with mathematical certainty, that every alert your tools generate is being fully investigated.
The question you need to answer
Can you demonstrate that your SOC triages every alert to the depth required to detect a sophisticated adversary?
If the answer is no, you’re carrying that risk today, and it compounds daily.
Want the full analysis — including the staffing math across alert volumes from 500 to 20,000 per day and a complete ROI breakdown? Download the whitepaper.
D3 Security’s Morpheus platform delivers AI-autonomous SOC triage powered by a cybersecurity-trained LLM and Attack Path Discovery. To quantify your organization’s triage gap, contact us for a tailored assessment.
The post 6 Minutes and a Prayer: The Math Your SOC Doesn’t Want You to See appeared first on D3 Security.
*** This is a Security Bloggers Network syndicated blog from D3 Security authored by Shriram Sharma. Read the original post at: https://d3security.com/blog/6-minutes-and-a-prayer/
如有侵权请联系:admin#unsafe.sh