
A China-linked threat actor tracked as 'PlushDaemon' is hijacking software update traffic u 2025-11-19 10:15:22 Author: www.bleepingcomputer.com(查看原文) 阅读量:9 收藏

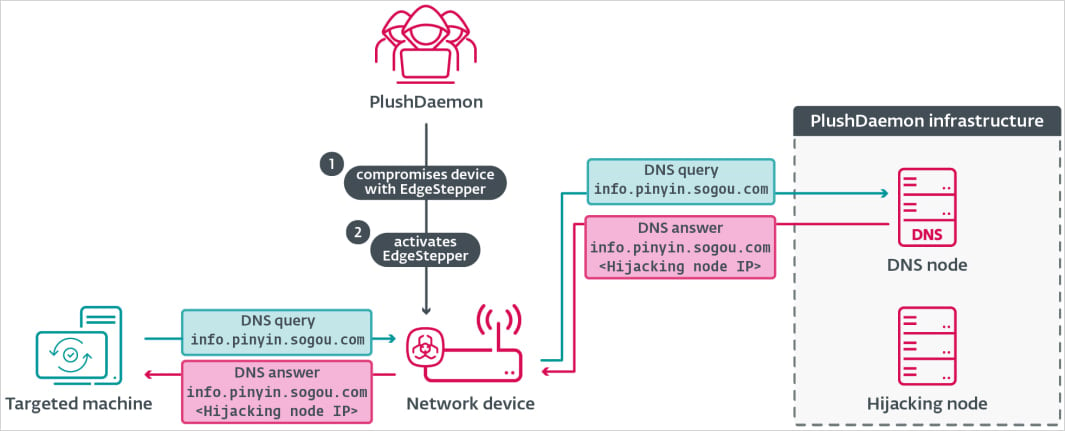
A China-linked threat actor tracked as 'PlushDaemon' is hijacking software update traffic using a new implant called EdgeStepper in cyberespionage operations.
Since 2018, PlushDaemon hackers have targeted individuals and organizations in the United States, China, Taiwan, Hong Kong, South Korea, and New Zealand with custom malware, such as the SlowStepper backdoor.
PlushDaemon has compromised electronics manufacturers, universities, and a Japanese automotive manufacturing plant in Cambodia. Telemetry data from cybersecurity firm ESET indicates that since 2019, the threat actor has relied on malicious updates to breach target networks.
.jpg)
Source: ESET
Attack chain
The attackers gain access to routers by exploiting known vulnerabilities or weak admin passwords, install the EdgeStepper implant, and then redirect software-update traffic to their own infrastructure.
Developed in Golang and compiled as an ELF binary, EdgeStepper works by intercepting DNS queries and redirecting them to a malicious DNS node after confirming that the domain is employed for delivering software updates, ESET researchers explain in a report shared with BleepingComputer.
When a victim tries to update their software, they receive the first-stage malware downloader for Windows called LittleDaemon, which is disguised as a DLL file named ‘popup_4.2.0.2246.dll.’
Source: ESET
LittleDaemon establishes communication with the attacker's hijacking node and fetches a second malware dropper named DaemonicLogistics, which is decrypted and executed in memory.
In the next stage of the attack, the hackers use DaemonicLogistics to retrieve their signature backdoor, SlowStepper.
The backdoor has been previously documented in attacks against users of the South Korean VPN product IPany. During those attacks, users downloaded a trojanized installer from the vendor’s official website.
The SlowStepper malware enables hackers to collect detailed system information, execute extensive file operations, run commands, and use various Python-based spyware tools that can steal data from the browser, intercept keystrokes, and collect credentials.
ESET researchers said that they examined PlushDaemon's hijacking of Sogou Pinyin, a software input method that is very popular in China, but they observed other product updates being hijacked in the same way.
They note that the PlushDaemon's adversary-in-the-middle capabilities are strong enough "to compromise targets anywhere in the world."
The report published today includes technical details for all the newly uncovered malware as well as a set of indicators of compromise for files, IP addresses, and domains that PlushDaemon used in attacks that deeployed the EdgeStepper network implant.
7 Security Best Practices for MCP
As MCP (Model Context Protocol) becomes the standard for connecting LLMs to tools and data, security teams are moving fast to keep these new services safe.
This free cheat sheet outlines 7 best practices you can start using today.
如有侵权请联系:admin#unsafe.sh

