
JumpServer 存在连接令牌认证漏洞(CVE-2025-62712),低权限用户可获取所有用户的连接令牌并未经授权访问资产。CVSS 评分 9.6 分,PoC 已公开。受影响版本为 JumpServer < 3.10.19-lts 和 < 4.10.10-lts。建议用户尽快升级至修复版本或通过配置 Nginx 临时缓解风险。 2025-11-7 04:2:25 Author: securityboulevard.com(查看原文) 阅读量:40 收藏
Overview
Recently, NSFOCUS CERT detected that JumpServer issued a security bulletin to fix the JumpServer connection token improper authentication vulnerability (CVE-2025-62712); Due to improper authentication of JumpServer’s /api/v1/authentication/super-connection-token/hyper-connected endpoint, attackers with low-privilege accounts can obtain the connection tokens of all system users and connect to managed assets as them, thereby achieving unauthorized access and privilege escalation operations. The CVSS score 9.6, and PoC has been made public. Relevant users are requested to take measures for protection as soon as possible.
Reference link: https://github.com//jumpserver/jumpserver/security/advisories/GHSA-6ghx-6vpv-3wg7
Scope of Impact
Affected versions
- JumpServer < 3.10.19-lts
- JumpServer < 4.10.10-lt
Unaffected version
- JumpServer >= 3.10.20-lts
- JumpServer >= 4.10.11-lts
Risk Investigation of Exposure Surface
Cloud detection
NSFOCUS External Attack Surface Management Service (EASM) supports the Internet asset investigation of CVE-2025-62712 vulnerability risks. It has helped service customer groups complete exposure surface investigations and conduct vulnerability warnings and closed-loop disposal timely before threats occur. Interested customers can arrange detailed consultation and communication by contacting their local regional colleagues at NSFOCUS or sending an email to [email protected].
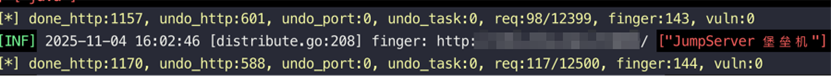
Tool troubleshooting
NSFOCUS Automated Penetration Testing Tool (EZ) supports fingerprint recognition and troubleshooting of JumpServer. Users can directly use the web module for scanning and detection:
Mitigation
Official upgrade
At present, the official has released a new version to fix this vulnerability. Affected users are requested to upgrade the version as soon as possible for protection.
Download link: https://github.com/jumpserver/jumpserver/tags
Other protective measures
If the relevant users are temporarily unable to perform upgrade operations, they can also modify the Nginx configuration to block the GET request of the super-connection-token API for temporary relief:
location = /api/v1/authentication/super-connection-token/ {
if ($request_method = GET) { return 405; } # Block GET explicitly
proxy_pass http://jumpserver_backend;
}
location = /api/v1/resources/super-connection-tokens/ {
if ($request_method = GET) { return 405; } # Block GET explicitly
proxy_pass http://jumpserver_backend;
}
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, a pioneering leader in cybersecurity, is dedicated to safeguarding telecommunications, Internet service providers, hosting providers, and enterprises from sophisticated cyberattacks.
Founded in 2000, NSFOCUS operates globally with over 4000 employees at two headquarters in Beijing, China, and Santa Clara, CA, USA, and over 50 offices worldwide. It has a proven track record of protecting over 25% of the Fortune Global 500 companies, including four of the five largest banks and six of the world’s top ten telecommunications companies.
Leveraging technical prowess and innovation, NSFOCUS delivers a comprehensive suite of security solutions, including the Intelligent Security Operations Platform (ISOP) for modern SOC, DDoS Protection, Continuous Threat Exposure Management (CTEM) Service and Web Application and API Protection (WAAP). All the solutions and services are augmented by the Security Large Language Model (SecLLM), ML, patented algorithms and other cutting-edge research achievements developed by NSFOCUS.
The post JumpServer Connection Token Improper Authentication Vulnerability (CVE-2025-62712) Notice appeared first on NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks..
*** This is a Security Bloggers Network syndicated blog from NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. authored by NSFOCUS. Read the original post at: https://nsfocusglobal.com/jumpserver-connection-token-improper-authentication-vulnerability-cve-2025-62712-notice/
如有侵权请联系:admin#unsafe.sh
