好的,我现在需要帮用户总结一篇文章,控制在100字以内。用户已经提供了文章内容和示例回复,所以我得先仔细阅读文章,理解其主要内容。 文章是David Hammond在ISC实习期间的日记,主要讲述了他在实习中使用honeypot进行日志分析的经历。他遇到了无法远程访问honeypot的问题,于是转而下载日志到Windows笔记本上,并使用PowerShell脚本处理这些日志。他详细介绍了如何编写脚本来搜索特定的恶意软件哈希值,并解释了脚本的工作原理。 接下来,我需要将这些信息浓缩到100字以内。首先,确定关键点:实习经历、honeypot日志分析、PowerShell脚本、解决远程访问问题的方法。 然后,组织语言,确保简洁明了。避免使用复杂的术语,同时涵盖所有重要信息。例如,可以提到他通过PowerShell处理日志,搜索特定哈希值,并解释了脚本结构。 最后,检查字数是否符合要求,并确保内容准确传达原文的核心信息。 </think> 大卫·汉密尔顿在ISC实习期间通过PowerShell脚本分析honeypot日志,搜索特定恶意软件哈希值。他详细介绍了脚本结构和功能,展示了如何利用PowerShell处理JSON日志文件并提取所需信息。 2025-11-6 02:27:25 Author: isc.sans.edu(查看原文) 阅读量:17 收藏
[This is a Guest Diary by David Hammond, an ISC intern as part of the SANS.edu BACS program]
My last college credit on my way to earning a bachelor's degree was an internship opportunity at the Internet Storm Center. A great opportunity, but one that required the care and feeding of a honeypot. The day it arrived I plugged the freshly imaged honeypot into my home router and happily went about my day. I didn’t think too much about it until the first attack observation was due. You see, I travel often, but my honeypot does not. Furthermore, the administrative side of the honeypot was only accessible through the internal network. I wasn’t about to implement a whole remote solution just to get access while on the road. Instead, I followed some very good advice. I started downloading regular backups of the honeypot logs on a Windows laptop I frequently had with me.
The internship program encouraged us to at least initially review our honeypot logs with command line utilities, such as jq and all its flexibility with filtering. Combined with other standard Unix-like operating system tools, such as wc (word count), less, head, and cut, it was possible to extract exactly what I was looking for. I initially tried using more graphical tools but found I enjoy "living" in the command line better. When I first start looking at logs, I was not always sure of what I’m looking for. Command line tools allow me to quickly look for outliers in the data. I can see what sticks out by negating everything that looks the same.
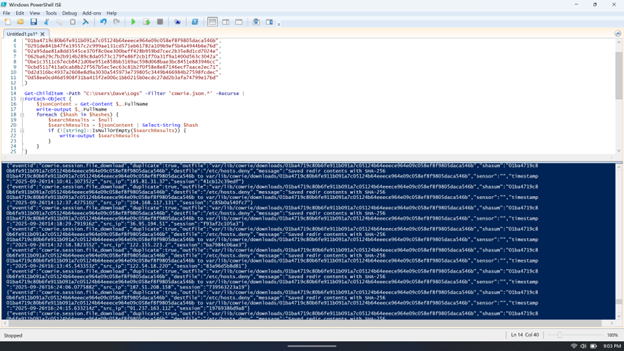
So, what’s the trouble? None of these tools were available on my Windows laptop. Admittedly, most of what I mention above are available for Windows, but my ability to install software was restricted on this machine, and I knew that native alternatives existed. At the time I had several directories of JSON logs, and a long list of malware hash values corresponding to an attack I was interested in understanding better. Here’s how a few lines of PowerShell can transform scattered honeypot logs into a clear picture of what really happened.
First, let’s start with the script in two parts. Here’s the PowerShell array containing malware hash values:
$hashes = @(
"00deea7003eef2f30f2c84d1497a42c1f375d802ddd17bde455d5fde2a63631f",
"0131d2f87f9bc151fb2701a570585ed4db636440392a357a54b8b29f2ba842da",
"01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b",
"0291de841b47fe19557c2c999ae131cd571eb61782a109b9ef5b4a4944b6e76d",
"02a95dae81a8dd3545ce370f8c0ee300beff428b959bd7cec2b35e8d1cd7024e",
"062ba629c7b2b914b289c8da0573c179fe86f2cb1f70a31f9a1400d563c3042a",
"0be1c3511c67ecb8421d0be951e858bb3169ac598d068bae3bc8451e883946cc",
"0cbd5117413a0cab8b22f567b5ec5ec63c81b2f0f58e8e87146ecf7aace2ec71",
"0d2d316bc4937a2608e8d9a3030a545973e739805c3449b466984b27598fcdec",
"0d58ee0cd46d5908f31ba415f2e006c1bb0215b0ecdc27dd2b3afa74799e17bd"
)
The $hashes = @( ) between quoted, comma-separated values, establishes a PowerShell array of strings which represents the hashes we want to search for. Now let’s look at how we put this array to use.
Get-ChildItem -Path "C:\Users\Dave\Logs" -Filter 'cowrie.json.*' -Recurse |
ForEach-Object {
$jsonContent = Get-Content $_.FullName
write-output $_.FullName
foreach ($hash in $hashes) {
$searchResults = $null
$searchResults = $jsonContent | Select-String $hash
if (![string]::IsNullOrEmpty($searchResults)) {
write-output $searchResults
}
}
}
Let's walk through the execution of the script. The first statement, Get-ChildItem, recurses every folder in the specified path (C:\Users\Dave\Logs\) and passes along all filenames that match the filter argument. Each filename is passed through the "pipe" (|) directly into the first ForEach-Object statement. You can see what’s passed by observing the output of the write-output $_.FullName line. The $_ is a variable designation which represents whatever is passed through the pipe. In this case, we know what kind of data to expect (a filename) so we can access it’s attribute, "FullName". This tells us the specific JSON log file currently being searched.
Now let’s get into the meat of the script. The main body of the script contains two nested For-Loops. The outer loop begins with the first "ForEach-Object" block of code. The inner loop is described by the lowercase "foreach" block. We already know the name of the JSON log we’ll be searching next, so the next line, $jsonContent = Get-Content $_.FullName sets that up to happen. It takes the content of the first filename passed to $_ though the pipe, reads the contents of that filename, and stores the text in a variable named $jsonContent. Now we’ve got our first log to search, all we have to do is run through the list of hash values to search for! This takes us to the point of the script where we reach the inner-loop. The foreach inner-loop is similar to the outer loop with the exception of how it processes data. The statement, foreach ($hash in $hashes) takes each hash value found in the $hashes array and puts a copy of it into $hash before executing the code block it contains.
When the inner-loop runs it does three things. First, $searchResults = $null empties the value of the $searchResults variable. This is also called "initializing" the variable, and it’s a good practice whenever you're working with loops that re-use the same variable names. Second, with the variable clear and ready to accept new values, the next line accomplishes a few things.
$searchResults = $jsonContent | Select-String $hash
Starting to the right of the equals sign, we’re passing the JSON log text $jsonContent into the command "Select-String" while also passing Select-String a single argument, $hash. Remember earlier when the lowercase foreach loop started, it takes each value found in the $hashes array and (one at a time) places their values into $hash before executing the block of code below it. So we’re passing the text in $jsonContent through another pipe to Select-String, which takes that text and searches for the value $hash within the contents of $jsonContent. The results of Search-String are then stored in the variable named $searchResults.
if (![string]::IsNullOrEmpty($searchResults)) {
write-output $searchResults
}
Third and finally, we have an if statement to determine whether the prior Select-String produced any results. If it found the $hash value it was looking for, the $searchResults variable will contain data. If not, it will remain empty ($null). The if statement makes that determination and prints the $searchResults it found. Note the ! at the beginning of the statement which tells it to evaluate as, "if not empty."

While compact in size, this script introduces the PowerShell newcomer to a variety of useful functions: traversing files and folders, retrieving text, searching text, and nested loops are all sophisticated techniques. If you save this script, you can adapt it in many ways whenever a quick solution is needed. Understanding the tools that are available to us in any environment and having practice adapting those tools to our circumstances makes us all better cybersecurity professionals.
[1] https://www.sans.edu/cyber-security-programs/bachelors-degree/
-----------
Guy Bruneau IPSS Inc.
My GitHub Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu
如有侵权请联系:admin#unsafe.sh