The notorious Lazarus Group actors exploited a recently patched privilege escalation flaw in the Windows Kernel as a zero-day to obtain kernel-level access and disable security software on compromised hosts.
The vulnerability in question is CVE-2024-21338 (CVSS score: 7.8), which can permit an attacker to gain SYSTEM privileges. It was resolved by Microsoft earlier this month as part of Patch Tuesday updates.
"To exploit this vulnerability, an attacker would first have to log on to the system," Microsoft said. "An attacker could then run a specially crafted application that could exploit the vulnerability and take control of an affected system."
While there were no indications of active exploitation of CVE-2024-21338 at the time of the release of the updates, Redmond on Wednesday revised its "Exploitability assessment" for the flaw to "Exploitation Detected."
Cybersecurity vendor Avast, which discovered an in-the-wild admin-to-kernel exploit for the bug, said the kernel read/write primitive achieved by weaponizing the flaw allowed the Lazarus Group to "perform direct kernel object manipulation in an updated version of their data-only FudModule rootkit."
The FudModule rootkit was first reported by ESET and AhnLab in October 2022 as capable of disabling the monitoring of all security solutions on infected hosts by means of what's called a Bring Your Own Vulnerable Driver (BYOVD) attack, wherein an attacker a driver susceptible to a known or zero-day flaw to escalate privileges.
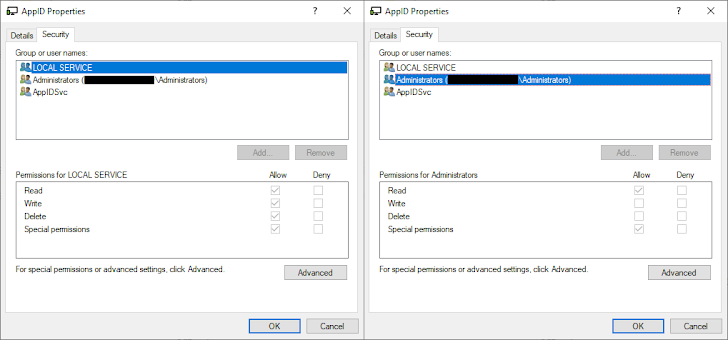
What makes the latest attack significant is that it goes "beyond BYOVD by exploiting a zero-day in a driver that's known to be already installed on the target machine." That susceptible driver is appid.sys, which is crucial to the functioning of a Windows component called AppLocker that's responsible for application control.
The real-world exploit devised by the Lazarus Group entails using CVE-2024-21338 in the appid.sys driver to execute arbitrary code in a manner that bypasses all security checks and runs the FudModule rootkit.
"FudModule is only loosely integrated into the rest of Lazarus' malware ecosystem and that Lazarus is very careful about using the rootkit, only deploying it on demand under the right circumstances," security researcher Jan Vojtěšek said, describing the malware as under active development.
Besides taking steps to sidestep detection by disabling system loggers, FudModule is engineered to turn off specific security software such as AhnLab V3 Endpoint Security, CrowdStrike Falcon, HitmanPro, and Microsoft Defender Antivirus (formerly Windows Defender).
The development marks a new level of technical sophistication associated with North Korean hacking groups, continuously iterating its arsenal for improved stealth and functionality. It also illustrates the elaborate techniques employed to hinder detection and make their tracking much harder.
The adversarial collective's cross-platform focus is also exemplified by the fact that it has been observed using bogus calendar meeting invite links to stealthily install malware on Apple macOS systems, a campaign that was previously documented by SlowMist in December 2023.
"Lazarus Group remains among the most prolific and long-standing advanced persistent threat actors," Vojtěšek said. "The FudModule rootkit serves as the latest example, representing one of the most complex tools Lazarus holds in their arsenal."
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.